دانلود مقاله بررسی اجمالی الگوریتم های رمزگذاری در تصاویر رنگی
چکیده
این روزها امنیت در امر انتقال داده ها از اهمیت ویژه ای برخوردار است. تصاویر جزو جذاب ترین داده ها در حوزه رمزگذاری می باشند. تصاویر رنگی از جذابیت بیشتری نسبت به تصاویر خاکستری برخوردار هستند زیرا اطلاعات بیشتری را ارائه می دهند. در این مقاله، چندین طرح رمزگذاری برای تصاویر رنگی (حالت RGB) بر اساس حوزه های بکارگیری بصورت گسترده مورد بررسی قرار گرفته شده است، بعلاوه در این زمینه بالغ بر 50 مقاله که بیشترشان سال پیش منتشر شده اند در اینجا خلاصه شده اند. همچنین، در این مقاله رمزگذاری تصاویر رنگی به ده طرح دسته بندی شده اند، و سپس طرح های پیشنهادی مقایسه شده و مزایا و محدودیت هایشان مشخص شده است. بعلاوه، لیست کاملی از تکنیک های آنالیز امنیتی متداول برای رمزگذاری تصاویر (خاکستری یا رنگی) که توانایی ارزیابی مقاومت بالقوه این روش در مقابل حملات احتمالی مختلف را دارند مورد بحث قرار گرفته اند. هدف از این مقاله ارائه اطلاعات دقیق در مورد طرح های رمزگذاری فعلی در حوزه تصاویر RGB می باشد. و در آخر، در این مقاله چندین مسئاله و مسیر تحقیقاتی به منظور اکتشاف در حوزه های امیدوار کننده برای پیشرفت های آتی در نظر گرفته شده اند.
1. مقدمه
انتقال داده ها در شبکه های ارتباطی مختلف باعث حساسیت امنیت داده های چندرسانه ای شده است. سابقا، رمزگذاری متن با استفاده از روشهایی مانند RSA (توسعه داده شده توسط، ریوست، شامیر و ادلمن)، استاندارد رمزگذاری داده ها (DES)، استاندارد پیشرفته رمزگذاری (AES)، و الگوریتم بین المللی رمزگذاری داده ها (IDEA) صورت می گرفت، هرچند رمزگذاری تصویر دارای تفاوتهایی نسبت به رمزگذاری متن می باشد چنانکه برخی خصوصیات ذاتی مانند افزونگی بالا و یا حجم بالای داده ها فقط در تصاویر وجود دارند (1). بعلاوه روش های رمزگذاری متن دارای سرعت و قدرت کافی در پخش و تغییر داده های تصاویر نبودند (2). تصاویر دیجیتالی که دارای حجم بزرگی از اطلاعات می باشند، دلیل بزرگی مقیاس تصویر هستند (3). درکل، از دو رویکرد اصلی برای حفاظت از تصاویر دیجیتالی استفاده شده است: پنهان کاری اطلاعات که شامل علامت نگاری، ناشناس بودن، استگانوگرافی، و پوشش شبکه و رمزگذاری که شامل رمزگذاری مرسوم و سایر روشهایی مانند رمزگذاری بی نظم می باشد (4).
مهرا و همکاران (5-7) یک تکنیک ادغام اصلاح شده در حوزه تبدیل موجک ها ارائه داده اند. در روش پیشنهادی آنها، اجزای فرکانس های بالا و پایین با یکدیگر ترکیب می شوند تا کیفیت تصویر را بهتر کنند. همچنین برخلاف تکنیک رمزگذاری بصری نا متقارن بر پایه رویکرد برش فاز و دامنه، چهار کلید نا متقارن برای هر تصویر تولید می کند.
6. نتیجه گیری و جهت های آتی
امنیت تصاویر به یک هدف مهم در این عصر بدل گردیده است. تکنولوژی های شبکه ای و ارتباطی چندین حالت برای انتقال تصاویر در سطح دنیا ارائه داده اند. از تصاویر بصورت گسترده ای در زمینه های مختلف از جمله آموزش آنلاین، خدمات مهندسی، خدمات دفاعی، آزمایشات علمی، تصویربرداری پزشکی، ارائه هنر و یا تبلیغت استفاده می شود. با افزایش میزان استفاده از تکنیک های دیجیتال ارسال و ذخیره سازی تصاویر، مسئاله بنیادی حفاظت از تصاویر به دلیل محرمانه بودن، درستی و سندیت و عدم رد آن دارای اهمیت بالایی است. از آنجایی که تصاویر رنگی حامل اطلاعات بیشتری نسبت به تصاویر خاکستری هستند، امنیت تصاویر رنگی به مسئاله مهمی در زمینه امنیت اطلاعات تبدیل شده است. چندین رویکرد برای رمزگذاری تصاویر ارائه شده است. طرح های رمزگذاری تصاویر رنگی در این مقاله مشخص شده و از لحاظ نوع استفاده مورد بررسی قرار گرفته اند. چندین تکنیک رمزگذاری تصاویر در این مقاله مطرح شده است. بعلاوه لیست کاملی از تکنیک های آنالیز امنیتی در این مقاله (خاکستری یا رنگی) ارائه و مورد بحث قرار گرفته اند، و مقاومت بالقوه روش ها در مقابل حملات مختلف ارزیابی شده است. همچنین مقایسه ای کامل از طرح های پیشنهادی ارائه شده است، که می تواند در طراحی الگوریتم های رمزگذاری آتی تصاویر بسیار مفید باشد.
جهت فعلی رمزگذاری تصاویر رنگی طراحی یک روش ایمن با کمترین عوامل است که در مقابل حملات امنیتی ایمن بوده و دارای ویژگی های ایده آل مطرح شده در بخش 5 باشد. بعلاوه، با توجه به اهمیت پوشیدگی کلید محرمانه در رمزگذاری تصاویر؛ در تمامی مقالاتی که از طرح های پیشنهادی استفاده کرده اند از چندین روش برای به هم زدن کلید محرمانه استفاده شده است. بنابراین، در تحقیقات آتی طراحی رمزگذاری ایمن تصاویر رنگی می بایست مد نظر گرفته شود. همچنین، استفاده از روش های تکاملی و نامنظم در تمامی رمزگذاری ها ضروری است، تا آنها بتوانند با ترکیب با سایر طرح ها نقوص خود را مرتفع کنند.
Abstract
Nowadays, security in data transfer is of special importance. Images are of the most attractive kinds of data in the encryption domain. Color images are more attractive than the gray-level images due to provision of more information. In the present study, various existing color (RGB mode) image encryption schemes have been examined comprehensively based on the application domains in addition to summarizing over 50 studies in this field, most of which being published in the last year. In addition, in this study, color image encryption has been categorized into ten schemes, then the proposed schemes have been compared and their advantages and limitations have been highlighted. Moreover, a complete list of common security analysis techniques for (gray or color) image encryption has been discussed which are capable of evaluating the method potential resistance to different possible attacks. The present study has been carried out to provide detailed knowledge regarding the existing image encryption schemes in the area of the RGB images. Finally, in the current study, various open issues and research directions have been considered in order to explore the promising areas for future developments.
1. Introduction
Data transmission on various communication networks has led to the sensitivity of the security of multimedia data. Previously, text encryption was conducted through methods such as RSA (developed by Rivest, Shamir and Adleman), Data Encryption Standard (DES), Advanced Encryption Standard (AES), and International Data Encryption Algorithm (IDEA), however image encryption differs from text encryption as some intrinsic characteristics including high redundancy or bulky data capacity are merely present in images [1]. In addition, text encryption methods lacked sufficient speed and power in diffusing and shuffling the image data [2]. Digital images carrying a huge volume of information account for large proportion [3]. Overall, there are two main approaches exploited to protect digital images: information hiding including watermarking, anonymity, steganography, and cover channel, and encryption including conventional encryption and other methods such as chaotic encryption [4].
Mehra et al. [5–7] presented a modified fusion technique in wavelet transform domain. In their proposed method, low and high frequency components are merged together to improve the image content. Also unlike optical asymmetric encryption technique based on phase- and amplitude-truncation approach, it generated four asymmetric keys corresponding to each image.
6. Conclusion and future directions
Security of images has become an important agenda of the present era. Network and communication technologies provide several modes for transferring images worldwide. Images are frequently used in various fields including online learning, engineering services, defense services, scientific experiments, medical imaging, art exhibition, or advertising. With the increased use of digital techniques for transmitting and storing images, the fundamental issue of protecting images for confidentiality, integrity, authentication, and non-repudiation are of major concerns. Since the color images carry richer information compared to the gray-level ones, color image security has become an important issue in the field of information security. Several approaches have been proposed for encrypting images. The color image encryption schemes have been outlined and examined in the present study in terms of usage. Several image encryption techniques have been proposed in the literature. Moreover, a complete list of the common security analysis techniques was presented in the current study for (gray or color) image encryption and discussed, and the potential resistance of the methods to different possible attacks was assessed. Moreover, a complete comparison of these proposed schemes was provided, which can be very useful in designing the future image encryption algorithms for color images.
The ongoing direction in the color image encryption is designing a secure method with the least possible factors for resistance against the security attacks and inclusion of the ideal properties specified in Section 5. Furthermore, considering the privacy of the secret keys is very important in image encryption; however in all of the studies employing the proposed schemes, various methods have been used for scrambling the secret keys. Therefore, designing secure color image encryption should be taken into account in the future investigations. In addition, the use of evolutionary and chaotic methods is highly necessary in all encryption applications, so that they need to be integrated with other schemes to compensate for their deficiencies.
چکیده
1. مقدمه
2. رمزگذاری تصویر: یک بررسی اجمالی
3. طرح های رمزگذاری تصاویر رنگی
3.1. رمزگذاری تصاویر رنگی با استفاده از الگوریتم های مبتنی بر بی نظمی
3.2 رمزگذاری تصاویر رنگی با استفاده از جابجایی
3.3. رمزگذاری بصری تصاویر رنگی
3.4 رمزگذاری تصاویر رنگی بر اساس DNA
3.5. رمزگذاری تصاویر رنگی بر اساس حوزه فرکانس
3.6. رمزگذاری تصاویر رنگی بر اساس آمیزش
3.7. رمزگذاری تصاویر رنگی با استفاده از روش های تکاملی
3.8. رمزگذاری تصاویر رنگی با تجزیه سطوح بیتی
3.9. رمزگذاری دوگانه (چندگانه) تصویر برای تصاویر رنگی
3.10. رمزگذاری تصاویر رنگی با استفاده از تحول مخلوطی
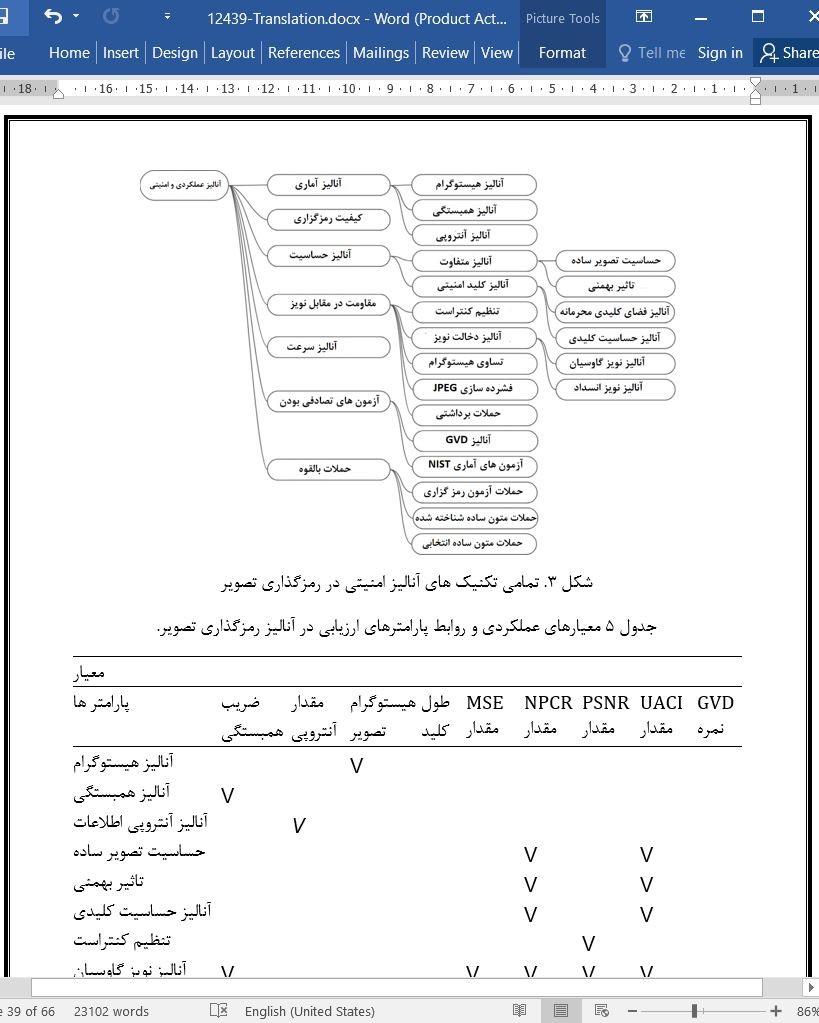
4. معیارهای ارزیابی عملکرد
4.1 معیار های عملکرد
4.2 مقایسه
5. بحث
6. نتیجه گیری و جهت های آتی
منابع
ABSTRACT
1. Introduction
2. Image encryption: a brief review
3. Color image encryption schemes
3.1. Color image encryption using chaos-based algorithms
3.2. Color image encryption using permutation
3.3. Optical color image encryption
3.4. DNA based color image encryption
3.5. Frequency domain based color image encryption
3.6. Hash based color image encryption
3.7. Color image encryption using evolutionary methods
3.8. Color image encryption using bit plane decomposition
3.9. Double (multiple)-image encryption for color images
3.10. Color image encryption using scrambling transform
4. Performance evaluation measures
4.1. Performance metrics
4.2. Comparison
5. Discussion
6. Conclusion and future directions
References
- ترجمه فارسی مقاله با فرمت ورد (word) با قابلیت ویرایش، بدون آرم سایت ای ترجمه
- ترجمه فارسی مقاله با فرمت pdf، بدون آرم سایت ای ترجمه