دانلود مقاله حملات منع سرویس در سطح لایه کاربردی: طبقه بندی و بررسی
چکیده
اخیرا افزایش حملات منع سرویس (DoS) در سطح لایه کاربردی، توجه زیادی را از سمت جوامع پژوهشی حوزه امنیت به سمت خود جلب کرده است. از انجاییکه حملات DoS در سطح لایه کاربردی معمولا خود را در سطح شبکه نشان نمیدهند، مانع شناسایی شبکه لایه-محور سنتی میگردند. بنابراین، جوامع پژوهشی تمرکزشان را روی شناسایی حملات DoS در سطح لایه کاربردی خاص و مکانیسمهای کاهش آن قرار میدهند. به هر حال، ایجاد مکانیسمهای دفاعی کارامد و موثر در برابر چنین حملاتی، نیازمند درک کاملی از حملات کنونی DoS در سطح لایه کاربردی تحت شرایط یکپارچه است. بنابراین، در این مقاله ما این موضوع را مد نظر قرار داده و طبقه بندی حملات DoS در سطح لایه کاربردی مطرح را میکنیم. از طریق طراحی این طبقه بندی پیشنهادی، پژوهشگران درک بهتری از این حملات بدست اورده و مبنایی برای سازماندهی تلاشهای پژوهشی در این حوزه خاص صورت میگیرد.
1. مقدمه
تعداد و قدرت حملات منع سرویس (DoS) در سه ماهه اول سال 2013، به عنوان بدترین دوره سه ماهه تاریخ حملات DoS شناخته میشود (پرولکسیس، 2013) . به دنبال بهبود فناوریهای شبکه پرسرعت و باتنتها ، حملات DoS مدرن از مقیاس 100 Gbps (100 گیکا بیت در ثانیه) فراتر رفته و تبدیل به مهمترین تهدید در حوزه اینترنت شده است. حملات DoS که به عنوان یکی از قدیمیترین نوع حملات هستند، به دلیل ایجاد اختلال و قابلیت تخلیه منابع محاسباتی یا پهنای باند قربانیان در عرض چند دقیقه، شناخته شده هستند. به دلیل سادهبودن نحوه عملکرد ان، این نوع حملات به دلیل میزان حملات دینامیک و حجیمشان به سادگی قابل تشخیص هستند. در نتیجه، در سالهای اخیر شاهد روند پیشرفت به سمت حملات DoS در سطح لایههای کاربردی پیچیدهتری بودهایم.
در مقایسه با حملات سنتی DoS، حملات DoS در سطح لایه کاربردی به صورت مخفی، پیچیده و غیرقابلشناسایی در لایه شبکه است ( ژی و یو 2009). با تمرکز روی خصوصیات ویژه و آسیبپذیری پروتکلهای لایه کاربردی، حملات DoS در سطح لایه کاربردی، دارای قابلیت آلودهسازی سطوح مشابهی همچون سیل حملات DoS سنتی با هزینه پایینتر، است.
به دنبال افزایش اخیر حملات DoS در سطح لایه کاربردی، جوامع پژوهشی تمرکزشان را روی تکنینکهای دفاعی و کاهشی این نوع از حملات قرار دادهاند. از آنجایی که دفاع موثر نیازمند درک جامعی از حملات DoS در سطح لایه کاربردی دارد، چندین پژوهش کنونی در این حوزه تلاش کرده است تا به دسته بندی این حملات بپردازد.
5. نتیجهگیری و پزوهشهای آینده
این مقاله به معرفی دستهبندی حملات DoS در سطح لایه کاربردی به همراه چند مثال بارز آن از لحاظ صنعتی و علمی میپردازد تا مبنایی را برای سازماندهی تلاشهای پژوهشی در حوزه حملات DoS در سطح لایه کاربردی ایجاد کند. انگیزهای که در ورای این تلاشها وجود دارد به عنوان یک ضرورت برای درک کامل حملات DoS در سطح لایه کاربردی است، که تحت حمایت اصطلاحات یکپارچهای قرار گرفته، و امکان بکارگیری مکانیسمهای دفاعی کارآمد و موثری را علیه این حملات ایجاد میکند. این فرایند ضروری است به این دلیل که شناسایی و کاهش این حملات به عنوان یک مسئله چالشبرانگیز است. این حملات در مقایسه با حملات DOS در سطح لایه شبکه پیچیدهتر و مخفیتر هستند، که منجر به جابه جایی تحت نظارت سیستمهای شناسایی نفوذ مبتنی بر لایه شبکه میگردند.
علاوه بر این، از طریق طراحی این دستهبندی پیشنهادی، تعدادی از مشخصههای کلیدی حملات DoS در سطح لایه کاربردی تعریف میگردد تا تغییرپذیری این جملات را مشخص کنند. مشخصههای تعریفشده، به توصیف مراحل کلی حمله (یعنی شناسایی و اجرا)، ویژگیهای حمله و تاثیرات حمله روی سیستم مورد هدف میپردازند. این مشخصهها یک نقشه راهی را برای محققان ایجاد میکنند تا به هدایت تنوع حملات DoS در سطح لایه کاربردی و متعاقب ان ایجاد مبنایی برای دسته بندی پیشنهادی بپردازند.
در مورد پژوهشهای اینده، به دنبال تعریف مجموعهای از معیارهای سنجش مناسب برای مشخصههای اقتباسی هستیم. این معیار سنجشی تعریفشده برای ارزیابی مکانیسمهای دفاعی بلقوه در برابر حملات DoS در سطح لایه کاربردی ضروری هستند. بعلاوه، معیارهای سنجشی تعریفشده میتواند به عنوان پارامتری در بررسی حملاتی که تا به حال ظاهر نشده ولی میتواند به عنوان تهدیدات بلقوهای در اینده باشند، مورد استفاده قرار گیرد. در نهایت، مجموعهای از این معیارهای سنجشی تعریفشده میتواند در طراحی و بکارگیری مکانیسمهای دفاعی در برابر حملات DoS در سطح لایه کاربردی، مورد استفاده قرار گیرد.
Abstract
The recent escalation of application-layer denial of service (DoS) attacks has attracted a significant interest of the security research community. Since application-layer DoS attacks usually do not manifest themselves at the network level, they avoid traditional network-layer-based detection. Therefore, the security community has focused on specialised application-layer DoS attacks detection and mitigation mechanisms. However, the deployment of reliable and efficient defence mechanisms against these attacks requires the comprehensive understanding of the existing application-layer DoS attacks supported by a unified terminology. Thus, in this paper we address this issue and devise a taxonomy of application-layer DoS attacks. By devising the proposed taxonomy, we intend to give researchers a better understanding of these attacks and provide a foundation for organising research efforts within this specific field.
1 Introduction
The frequency and power of denial-of-service (DoS) attacks have marked the first quarter of 2013 as the worst quarter for DoS attacks in history (Prolexic, 2013). Leveraging botnets and high-speed network technologies, modern DoS attacks exceed the scale of 100 Gbps becoming a major threat on the internet (Prolexic, 2013). Being one of the oldest type of attacks, DoS attacks are known for their disruptiveness and ability to deplete the computing resources and/or bandwidth of their victims in a matter of minutes. In spite of being trivial in execution, they are easily detectable mostly due to their dynamic and voluminous attack rates. As a result, the recent years have seen a growing trend towards more sophisticated application-layer DoS attacks.
As opposed to traditional DoS attacks, application layer DoS attacks are perceived as stealthy, sophisticated and undetectable at the network layer (Xie and Yu, 2009). Focusing on specific characteristics and vulnerabilities of application layer protocols, application layer DoS attacks are capable of inflicting the same level of impact as traditional flooding DoS attacks at a much lower cost.
With the latest escalation of application-layer DoS attacks, the research community has focused its attention on defence and mitigation techniques for this type of attacks. Since effective defences require a comprehensive understanding of the existing application-layer DoS attacks, several existing studies in the field attempted to provide some classification of these attacks.
5 Conclusions and future work
This paper presents a taxonomy of the existing application-layer DoS attacks accompanied with representative examples, derived from both industry and academia, in order to provide a foundation for organising research efforts in the field of application-layer DoS attacks. The incentive behind this effort has been the necessity for a comprehensive understanding of the existing application-layer DoS attacks, supported by a unified terminology, that will enable the advanced deployment of reliable and efficient defence mechanisms against these of attacks. This is essential due to the fact that the detection and mitigation of these attacks remain challenging issues. They are stealthier and more sophisticated compared to network-layer DoS attacks resulting in flying under the radar of traditional network-layer-based intrusion detection systems.
Furthermore, by devising the proposed taxonomy, a number of key features of application-layer DoS attacks is defined to characterise the variability of these attacks. The defined features describe the general steps of an attack (i.e., reconnaissance and execution), the attack characteristics and the attack effect on the targeted system. These features comprise a roadmap for researchers to navigate through the diversity of the application-layer DoS attacks and thus form a foundation of the proposed taxonomy.
As future work, we plan to define a set of proper metrics for the extracted features. The defined metrics will be essential for evaluating potential defence mechanisms against known application-layer DoS attacks. Moreover, the defined metrics can be used as parameters in the study of attacks that have not yet appeared but can be potential threats in the future. Finally, the set of the defined metrics can be used in the design and deployment of defence mechanisms against the new application-layer DoS attacks.
چکیده
1. مقدمه
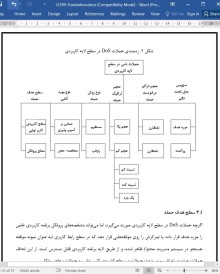
2. حملات DoS در سطح لایه کاربردی
3. ردهبندی حملات DoS در سطح لایه کاربردی
3.1 سطح هدف حمله
3.2 نوع سوءاستفاده
3. نوع روش حمله
3.4 حجم ترافیک حمله
3.5 تراکم کار درخواست حمله
3.6 سرویسهای تحت تاثیر واقع شده
4. نمونههایی از حملات DoS در سطح لایه کاربردی
4.1 حملات سطح کاربردی کاربر نهایی
4.2 حملات سطح پروتکل
4.2.1 حملات مبتنی بر HTTP
4.2.2.1 حمله از نوع ارسال کند HTTP
4.2.1.2 حمله از نوع خوانش کند HTTP
4.1.2.3 حملات مبتنی بر DNS
4.1.2.4 حملات مبتی بر SIP
4.1.2.5 حملات مبتنی بر SSL
5. نتیجهگیری و پزوهشهای آینده
منابع
Abstract
1 Introduction
2 The application-layer DoS attacks
3 Taxonomy of application-layer DoS attacks
3.1 Attack target level
3.2 Exploitation type
3.3 Attack methodology type
3.4 Attack traffic volume
3.5 Attack requests’ workload
3.6 Affected services
4 Examples of application-layer DoS attacks
4.1 End-user application level attacks
4.2 Protocol level attacks
4.2.1 HTTP-based attacks
4.2.1.1 Slow HTTP sent attack
4.2.1.2 Slow HTTP read attack
4.1.2.3 DNS-based attacks
4.1.2.4 SIP-based attacks
4.1.2.5 SSL-based attacks
5 Conclusions and future work
References
- اصل مقاله انگلیسی با فرمت ورد (word) با قابلیت ویرایش
- ترجمه فارسی مقاله با فرمت ورد (word) با قابلیت ویرایش، بدون آرم سایت ای ترجمه
- ترجمه فارسی مقاله با فرمت pdf، بدون آرم سایت ای ترجمه