دانلود مقاله امنیت در شبکه حسگر بی سیم
چکیده
شبکه حسگر بی سیم (WSN) برای خودکار سازی و بهبود قابلیتهای جمع آوری اطلاعات در پروژه های شاخصی از قبیل پایش پزشکی، صنایع، تحقیقات و آزمایشات علمی، کارخانه ها، حمل و نقل و غیره استفاده می شود. بازی واقعیت افزوده (AR )، واقعیت مجازی (VR)، دستگاه های پوشیدنی، شهرهای هوشمند، و کشاورزی هوشمند، برخی از برنامه های جدیدتر آن هستند. دولتها نیز در برنامه های نظامی خود، از شبکه حسگر بی سیم (WSN) برای جمع آوری داده ها و اطلاعات استفاده می کنند. گره های WSN در سطح گسترده ای استفاده می شوند، و از آنجاییکه ارزان، پودمانی، قابل برنامه ریزی، قابل پیکره بندی و اد هاک هستند، می توانند در یک محیط باز با اتصال بی سیم و غیره نیز استفاده شوند. این ویژگیها سبب شده که WSN به آسانی مورد حمله مهاجمان قرار بگیرد. داده های جمع آوری شده توسط WSN برای افراد یا سازمانها، داده های خصوصی یا حساسی هستند. از این رو، امنیت مسئله مهمی در تحقیقات WSN در نظر گرفته می شود. در این مقاله، یک مرور اجمالی بر امنیت WSN را ارائه می دهیم. ابتدا WSN و معماری آن را معرفی می کنیم. سپس، در مورد طبقه بندی لایه ای حملات امنیتی و تکنیکهای کاهشی محتمل به بحث می پردازیم تا بتوانیم حملات و شدت آنها را درک کنیم. برای حفظ امنیت WSN، الگوریتمهای رمزنگاری سبک وزن را از نظر شایستگی، عملکرد، نیاز به باتری و موارد دیگر مورد تحلیل و بررسی قرار می دهیم.
1. مقدمه
شبکه حسگر بی سیم (WSN)از یک دهه پیش معرفی شده است (1). منشا WSN را می توان مانند هر فن آوری رایانه ای دیگری به کاربردهای صنعتی سنگین و الزامات نظامی نسبت داد. WSN پیشینه ای بسیار قدیمی تر از اینترنت و حتی بسیاری از نسلهای رایانه دارد. اولین سیستمی که توانست از WSN مدرن تقلید کند، سیستم نظارت صوتی (SOSUS) (2) بود که در دهه 1950 توسط ارتش ایالات متحده طراحی شد. برای ردیابی و تشخیص زیردریاییهای شوروی از SOSUS استفاده می شد. علاوه بر این، برنامه شبکه حسگر توزیع شده (DSN) نیز با راه اندازی پروژه آژانس پروژه های تحقیقاتی پیشرفته دفاعی (DARPA) توسط دولت ایالات متحده، رسما در سال 1980 آغاز به کار کرد. پس از معرفی رسمی آن، علایق پژوهشی نسبت به آن بیشتر شد و تا حد زیادی مورد توجه آزمایشگاه های تحقیقاتی و افراد دانشگاهی قرار گرفت. بعدها DSN به WSN مدرن تغییر پیدا کرد. شکل اولیه WSN ، شبکه ای از حسگرهای توزیع شده در مناطق بزرگ یا کوچک جغرافیایی است که برای دریافت و جمع آوری هر نوع کمیت فیزیکی یا محیطی مانند دما، گرما، نور، رطوبت، صدا، ذرات معلق و غیره بکار برده می شود. داده هایی که توسط این حسگرهاجمع آوری می شوند به دستگاه مرکزی منتقل می شوند که به عنوان یک سینک عمل می کند. سپس، این داده ها از طریق شبکه توسط دستگاه مرکزی یا سینک به مقصد منتقل می شوند. حسگرها هزینه زیادی ندارند و به سادگی نصب می شوند و به همین دلیل در همان سالهای اول به کاربرد گسترده ای دست پیدا کردند. حسگرها از طریق امواج رادیویی با یکدیگر ارتباط برقرار می کنند. اکثر شبکه های WSN اد هاک هستند که در آنها حسگرها در مناطق جغرافیایی خاصی توزیع شده اند و گره ها نیز خودپیکربند هستند، بطوری که با یکدیگر ارتباط برقرار می کنند و خودشان با استفاده از استراتژیهایی مانند کمترین تعداد گره تا سینک، مسیری با گره های قدرتمند، مسیری با توان بالای باتری و غیره، بهترین مسیر را برای رسیدن به سینک تعیین می کنند. یک گره WSN متشکل از واحد پردازش مرکزی، یک واحد حسگر، یک واحد ارتباطی، و یک واحد قدرت می باشد. گره ها دستگاه های محاسباتی توان پایین یا کم قدرتی هستند که از باتری یا منبع انرژی استفاده می کنند و تنها هدفشان دریافت و جمع آوری داده ها و انتقال آنها به سینک است. از آنجاییکه گره ها در حال ساکن مسیریابی نمی شوند، و دائما نظارت یا حفاظت نمی شوند، در معرض طیف وسیعی از حملات قرار دارند.
7. نتیجه گیری
شبکه های حسگر بی سیم (WSN) در حال حاضر در همه جا وجود دارند. این شبکه ها به فن آوریهای آینده کمک میکنند تا از طریق حسگری، به قابلیتهای مقاوم به خطا و موثقی دست پیدا کنند. هم اکنون، WSN در انجام امور غیرهوشمند به اینترنت اشیا (IoT) کمک می کند. برنامه های جدیدتر WSN هر روزه افزایش می یابند و لازم است مورد تایید چارچوبهای امنیتی قرار بگیرند. ما به راحتی می توانیم بیشتر امور زندگی خود را با سپردن کارهای غیرضروری به ماشینها، بطور خودکار انجام دهیم، اما لازم است با بررسی و ایجاد تعادل بین آنها اطمینان حاصل کنیم که این سیستمها از نظر نشت داده های مهم یا طبقه بندی شده در معرض خطر قرار ندارند. امنیت بخش بزرگی از WSN است، اما هنوز یک معماری یا راه حل جامع برای آن تدوین نشده است. هدف این مطالعه این است که در شناسایی کارهایی که قبلا انجام شده و مسائل پیش رو در آینده به محققان آینده کمک کند. ما در این مقاله سعی کرده ایم دیدگاه جامعی از WSN را به همراه جدیدترین نوآوریها از لحاظ معماری، امنیت و مسیرهای پژوهشی آتی ارائه نماییم.
Abstract
Wireless Sensor Network (WSN) is used to enhance and automate the information capturing capabilities of critical projects such as Medical Monitoring, Scientific Experiments and Research, Industries, Factories, Transportation, etc. Wearable devices, Smart Cities, Smart Agriculture, Virtual Reality (VR), Augmented Reality (AR) gaming are some of its newer applications. Governments also use WSN to gather data for their military applications. WSN nodes have gained this massive adoption because they are cheap, modular, programmable, ad-hoc configurable, can operate in an open environment, wirelessly connected, etc. These features also make WSN easy to attack. Data captured by WSN are private or sensitive for individuals or organizations. Hence, security is one of the essential issues of research of WSN. In this paper, we present a current brief review of WSN Security. First, WSN and its architecture is introduced. Then, a layer-wise classification of security attacks and possible mitigation techniques are discussed to understand attacks and their severity. To secure WSN, lightweight cryptographic algorithms are analyzed for their suitability, performance, battery requirements, etc.
I. INTRODUCTION
Wireless Sensor Network (WSN) has a decade's old origin [1]. Like any computer technology, the origin of WSN is attributed to military requirements and heavy industrial applications. The history of WSN is much older than the Internet and even from most generations of computers. The first system that can mimic modern WSN was Sound Surveillance System (SOSUS) [2] developed in the 1950s by US Military. SOSUS was used to track and detect Soviet submarines. Further, with the establishment of the Defence Advanced Research Projects Agency (DARPA) project by the US Govt. Distributed Sensor Network (DSN) program was formally started in 1980. After its formal introduction, research interests started to rise and people from academics and research labs showed huge interest. Later DSN was modified into modern WSN. WSN in the most basic term, is a network of sensors spread over small or large geographical areas that are used to sense and collect any type of physical or environmental quantity like heat, temperature, light, sound, moisture, suspended particle matter etc.. The data collected via these sensors are transmitted to a central device, which acts as a sink. Central device or sink further transmit these data to its destination over the network. Sensors are cheap and easy to install, leading to WSN's huge adoption in its early years. Sensors communicate with each other using radio waves. Most WSN networks are Ad-Hoc networks in which sensors are scattered over the particular geographical area, and the nodes are self-configured such that they communicate with each other and determine the best path to reach the sink by themselves using strategies like lowest node count to sink, a path with high battery power, a path with powerful nodes etc. A WSN node comprises of central processing unit, a communication unit, a sensing unit, and a power unit. Nodes are low-powered (battery or energysource), low-power computation devices whose only purpose is to sense and collect data and transmit it to the sink. Since the nodes are not statically routed, constantly monitored or secured, they are susceptible to a large array of attacks.
VII. CONCLUSION
WSN networks are ubiquitous now. They are assisting future technologies to acquire reliant and fault-tolerant abilities through sensing. For now, WSN is assisting IoT in performing non-intelligent tasks. Newer applications of WSN are rising every day and security frameworks need to acknowledge that. We can easily automate most of our lives by leaving redundant tasks to machine, but there must be checks and balances to assure that these systems can't be compromised to leak important or classified data. Security is a big part of WSN, but a holistic architecture or solution is not developed yet. The study aims to assist future researchers in ascertaining the work done already and future issues to deal with. We tried to deliver the latest innovations and holistic view of WSN in terms of its security, architecture and future research directions.
چکیده
1. مقدمه
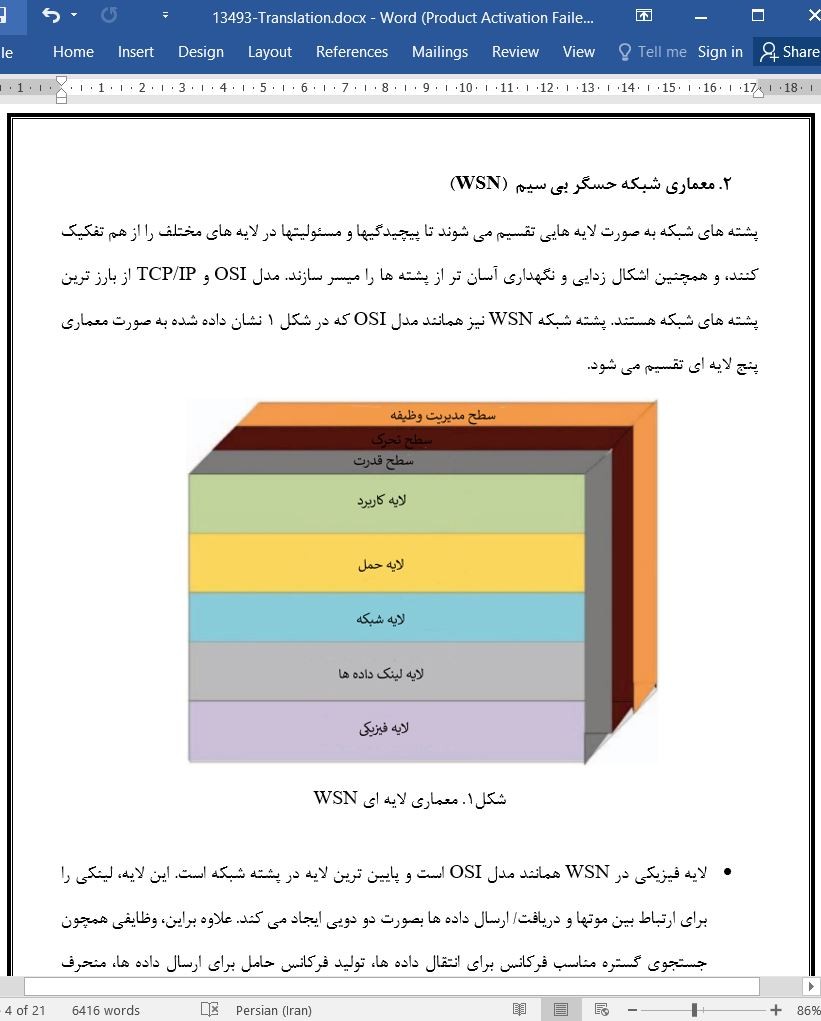
2. معماری شبکه حسگر بی سیم (WSN)
3. مسائل امنیتی شبکه حسگر بی سیم (WSN)
A. خود سازماندهی/ خود پیکره بندی
B. کنترل جریان
C. منابع محدود
D. محیط باز
E. تحرک گره ها
F. ناهمگنی گره ها
G. سیستم مرکزی
4. طبقه بندی لایه ای حملات به شبکه حسگر بی سیم (WSN)
A. لایه فیزیکی
B. لایه لینک داده ها
C. لایه شبکه
D. لایه حمل
E. لایه کاربرد
5. الگوریتمهای رمزنگاری سبک وزن
A. رمزهای بلوکی سبک وزن
B. رمزهای جریانی سبک وزن
c. الگوریتمهای هش سبک وزن و MAC
6. مسائل پژوهشی
7. نتیجه گیری
منابع
Abstract
I. INTRODUCTION
II. ARCHITECTURE OF WSN
III. SECURITY ISSUES OF WSN
A. Self-Configuration/Organization
B. Flow Control
C. Limited Resources
D. Open Environment
E. Mobility of nodes
F. Heterogeneity of Nodes
IV. LAYER-WISE CLASSIFICATION OF ATTACKS ON WSN
A. Physical Layer
B. Data Link Layer
C. Network Layer
D. Transport Layer
E. Application Layer
V. LIGHTWEIGHT CRYPTOGRAPHIC ALGORITHMS
A. Lightweight Block Ciphers
B. Lightweight Stream Ciphers
C. Lightweight Hash Algorithms and MAC
VI. RESEARCH ISSUES
VII. CONCLUSION
REFERENCES
این محصول شامل پاورپوینت ترجمه نیز می باشد که پس از خرید قابل دانلود می باشد. پاورپوینت این مقاله حاوی 16 اسلاید و 6 فصل است. در صورت نیاز به ارائه مقاله در کنفرانس یا سمینار می توان از این فایل پاورپوینت استفاده کرد.
در این محصول، به همراه ترجمه کامل متن، یک فایل ورد ترجمه خلاصه نیز ارائه شده است. متن فارسی این مقاله در 5 صفحه (1600 کلمه) خلاصه شده و در داخل بسته قرار گرفته است.
علاوه بر ترجمه مقاله، یک فایل ورد نیز به این محصول اضافه شده است که در آن متن به صورت یک پاراگراف انگلیسی و یک پاراگراف فارسی درج شده است که باعث می شود به راحتی قادر به تشخیص ترجمه هر بخش از مقاله و مطالعه آن باشید. این فایل برای یادگیری و مطالعه همزمان متن انگلیسی و فارسی بسیار مفید می باشد.
بخش مهم دیگری از این محصول لغت نامه یا اصطلاحات تخصصی می باشد که در آن تعداد 47 عبارت و اصطلاح تخصصی استفاده شده در این مقاله در یک فایل اکسل جمع آوری شده است. در این فایل اصطلاحات انگلیسی (تک کلمه ای یا چند کلمه ای) در یک ستون و ترجمه آنها در ستون دیگر درج شده است که در صورت نیاز می توان به راحتی از این عبارات استفاده کرد.
- ترجمه فارسی مقاله با فرمت ورد (word) با قابلیت ویرایش و pdf بدون آرم سایت ای ترجمه
- پاورپوینت فارسی با فرمت pptx
- خلاصه فارسی با فرمت ورد (word)
- متن پاراگراف به پاراگراف انگلیسی و فارسی با فرمت ورد (word)
- اصطلاحات تخصصی با فرمت اکسل