
دانلود رایگان مقاله بررسی کلاسهای متفاوت پروتکل های تصدیق RFID
چکیده:
سامانه بازشناسی با امواج رادیویی (RFID) تکنولوژی به روز و در حال پیشرفتی است. محدودیت های اصلی تکنولوژی RFID موارد امنیتی و حریم شخصی هستند. بسیاری از روش ها، از جمله رمزنگاری، تصدیق و تکنیکهای سخت افزاری، برای گذر از مشکلات امنیتی و حریم شخصی ارائه شده اند. این مقاله روی پروتکلهای تصدیق یا تایید متمرکز شده است. ترکیب محبوبیت تکنولوژِی RFID و نا امن بودن آن منجر به سیل پروتکلهای مشترک تصدیق شده است. پروتکلهای تصدیق به عنوان کامل، ساده، سبک و فوق سبک طبقه بندی می شوند. از سال 2002 تا به الان، تحقیقات مهمی انجام شده و پروتکلهای بسیاری نیز عرضه شده اند که برخی از این پروتکلها نیاز به ارتقا دارند. مقاله پیش رو پروتکلهای تصدیق مشترک RFID اخیرا ارائه شده را طبق کلاس تصدیق آن با جزئیات کامل بررسی می نماید. پروتکلهای که اکثرا بر اساس امنیت، تکنیک مقایسه شده اند مبتنی بر پروتکل هایی هستند که پروتکلهای ارائه شده با آنها و در نهایت، روش های تایید پروتکلها با یکدیگر مقایسه شده اند. نکات مهم این مقایسه در دو جدول تجمیع شده اند.
مقدمه:
سامانه بازشناسی با امواج رادیویی (RFID)
برای شناسایی اشیا با برچسبی کوچک در حال ایجاد است. این تکنولوژی به عنوان یکی از ضروری ترین تکنولوژی های این چند دهه قلمداد می شود . سیستمهای RFID از یک برچسب، یک برچسب خوان و یک سرور دیتابیس پشت خط تشکیل شده است. برچسب خوان شناساگر های نشگانگر های RFID را خوانده و هویت جستجو ها را برای سرور پشت خط می فرستند. اطلاعات بدست آمده از برچسب ورودی به پایگاه داده پشت خط خواهد بود.
برچسب ها در سه طبقه بسته به نوع تغذیه آنها دسته بندی میشوند: برچسب های فعال، نیمه فعال و غیر فعال. برچسب های RFID فعال نیازمند یک باتری داخلی برای تغذیه اجزای الکترونیکی خود و تولید سیگنال برای برچسب خوان هستند. برچسب های نیمه فعال و یا به عبارتی نیمه غیر فعال تنها از قدرت باتری برای روشن کردن مدار میکروچیپ استفاده می کنند و انرژی ساخت سیگنال پاسخ برای برچسب خوان را از سیگنال رادیویی برچسب خوان بدست می اورند. برچسب های غیر فعال تمام انرژی خود را از برچسب خوان بدست می آورند. علاوه بر این برچسب های RFID در سه بازه فرکانسی دسته بندی می شوند: فرکانس ضعیف(125-134KHz) فرکانس بالا(13.56KHz) و فرکانس فوق بالا(860-960KHz)]2[. برچسب های غیر فعال RFID (کم هزینه) که با پهنا های فرکانس فوق بالا کار می کنند امکان نو آوری را در حوزه های کاربرد روزانه، مثل ساخت اکسس کنترل، مدیریت زنجیره تجهیزات و موقعیت یابی کالا ها فراهم کرده اند. استاندارد کد الکترونیکی کالا(EPC) کلاس 1 (C1) نسل دوم(Gen2) مثالی از تکنولوژی های غیر فعال RFID است.
برخی متخصصین بر این باورند که بارکد های دیداری با برچسب های RFID ارزان قیمت متصل به کالاهای مورد مصرف جایگزین می شوند]4[. با این حال، به خاطر طبیعت رابطه بی سیم بین برچسب و برچسب خوان، این تکنولوژی تهدیدات بزرگی در زمینه امنیت و حریم شخصی دارد. پروتکل های تایید شده مشترک معمولا برای غلبه به حمله های امنیتی بین برچسب و برچسب خوان استفاده می شوند. از سال 2002 تحقیقات بسیاری انجام شده و پروتکلهای بی شماری ارائه شده اند اما برخی از آنها همچنان نیاز به ارتقا دارند.
در بخش هایی که در ادامه خواهیم خواند بخش 2 در مورد پروتکل های تایید شده و اهدف آنها بحث و توضیح خواهد داد. بخش 3 پروتکل ها را با توجه به طبقه خود بررسی و مقایسه می کند. بخش 4 مقایسه را ارزیابی می کند. بخش 5 نتایج حاصل از بررسی پروتکل های احراز هویت را ارائه می دهد.
2. پروتکل های تأیید شده
لوپز و همکاران [5] راه حل های بسیاری برای غلبه بر مسائل امنیتی و خطرات مرتبط با سیستم های RFID را معرفی کردند.در این مطالعه، ما قصد داریم تا پروتکل های تأیید شده را عمیق تر کنیم. تأییدیه اولین قدم در دفاع در مقابل حملات بی سیم به سیستم های RFID می باشد. هنگامی که سرور هویت برچسب RFID را تأیید می کند، اعتماد به برچسب آغاز می شود.پس از تاییده، خواننده می تواند به محتویات برچسب های تأیید شده دسترسی پیدا کند.
2.1 دسته های (کلاس های) پروتکل های تأیید شده
چین [6] اظهار داشت که پروتکل های تاییدی به چهار دسته با توجه به هزینه محاسبات برچسب و عملیات پشتیبانی شده تقسیم می شوند.
•پروتکل های کاملا پیشرفته: پروتکل هایی که از رمزگذاری متقارن و نامتقارن و تابع یک طرفه پشتیبانی می کند. مثالها در [7، 8] هستند.
•پروتکل های ساده: پروتکل هایی که از تابع هش و مولد عدد تصادفی پشتیبانی می کند (RNG). نمونه هایی از این دسته در [9، 10] ارائه شده است.
• پروتکل های سبک: پروتکل هایی که از بررسی افزونگی چرخه ای (CRC) و RNG پشتیبانی می کند. مثالها در [11-14] ارائه شده است.
• پروتکل فوق العاده سبک: پروتکل هایی که به ویژه برای دستگاه های بسیار محدود طراحی شده اند. اینها پروتکل ها فقط شامل عملیات ساده بیتی (مانند AND، OR، XOR) در برچسب ها می باشند. مثالها در [15، 16] داده شده است.
2.2 اهداف پروتکل های تأییدشده
با توجه به انواع تهدیدات بالقوه، یک پروتکل تاییدی، در هر دسته ای، باید همه یا بیشتر تهدیدها و خدمات امنیتی زیر را بررسی کند.
Abstract
Radio-frequency identification (RFID) is an up-and-coming technology. The major limitations of RFID technology are security and privacy concerns. Many methods, including encryption, authentication and hardware techniques, have been presented to overcome security and privacy problems. This paper focuses on authentication protocols. The combination of RFID technology being popular but unsecure has led to an influx of mutual authentication protocols. Authentication protocols are classified as being fully fledged, simple, lightweight or ultra-lightweight. Since 2002, much important research and many protocols have been presented, with some of the protocols requiring further development. The present paper reviews in detail recently proposed RFID mutual authentication protocols, according to the classes of the authentication protocols. The protocols were compared mainly in terms of security, the technique that they are based on, protocols that the presented protocol has been compared with, and finally, the method of verifying the protocol. Important points of the comparisons were collected in two tables.
1 Introduction
Radio-frequency identification (RFID) is being developed to distinguish the correct object with a small tag. This technology has been considered as one of the most substantial technologies of these decades [1]. RFID systems consist of a tag, a tag reader and a back-end database server. The reader reads the RFID tag’s identifier and sends the queried identity to the back end server. The information obtained from the tag is mostly an index to a back end database.
The tags are classified into three types according to how they are powered: active, semi-active and passive tags. Active RFID tags need internal batteries to power the electronic components and to create a reply signal to the reader. Semi-active tags or in other words semi-passive use batteries only for powering microchip’s circuit and they harvest energy to create a reply signal to the reader by using reader’s radio signal. Passive tags harvest their energy from the reader. RFID tags are also grouped into three basic frequency ranges: low frequency (125–134 kHz), high frequency (13.56 MHz) and ultrahigh frequency (860–960 MHz) ranges [2]. Passive (lowcost) RFID tags that operate in ultra-high-frequency bands have allowed innovation in several fields of daily application, such as building access control, supply chain management and goods tracking. The Electronic Product Code (EPC) Class1 (C1) Generation2 (Gen2) standard is an example of passive RFID technology [3].
Some experts believe that optical barcodes will be replaced with low-cost RFID tags attached to consumer items [4]. However, owing to the wireless nature of communication between the tag and reader, this technology has major security and privacy threats. Mutual authentication protocols are generally used to overcome security attacks between the reader and tags. Since 2002, much research has been conducted and numerous protocols are proposed but some of these still need to be developed further.
In the proceeding sections, Sect. 2 discusses and explains authentication protocols and their goals. Section 3 examines and compares protocols according to their class. Section 4 evaluates the comparison. Section 5 presents conclusions drawn from the review of authentication protocols.
2 Authentication protocols
Lopez et al. [5] presented many solutions to overcome the security issues and risks associated with the RFID systems. In this study, we aimed to deepen on authentication protocols. Authentication is the first step in defending against wireless attacks on RFID systems. Once the server validates the identity of the RFID tag, it begins trusting the tag. After authentication, the reader can access the contents of the authenticated tags.
2.1 Classes of authentication protocols
Chein [6] stated that authentication protocols are divided into four classes with accordance to the tag’s computational cost and supported operations.
• Fully fledged protocols: Protocols that support symmetric and asymmetric encryption, and a one-way function. Examples are in [7, 8].
• Simple protocols: Protocols that support hash function and random number generator (RNG). Examples of this class are given in [9, 10].
• Lightweight protocols: Protocols that support cyclic redundancy check (CRC) and RNG. Examples are given in [11–14].
• Ultra-lightweight protocols: Protocols that are tailored specially to extremely constrained devices. These protocols involve only simple bitwise operations (like AND, OR, XOR) on tags. Examples are given in [15, 16].
2.2 Goals of authentication protocols
Considering the variety of potential threats, an authentication protocol, whatever the class, should address all or most of the following security threats and services.
چکیده:
مقدمه:
سامانه بازشناسی با امواج رادیویی (RFID)
2. پروتکل های تأیید شده
2.1 دسته های (کلاس های) پروتکل های تأیید شده
2.2 اهداف پروتکل های تأییدشده
3. بررسی و مقایسه پروتکل های تأییدی
3-1- پروتکل های کاملا پیشرفته
3.2 پروتکل های ساده
3.3 پروتکل های سبک
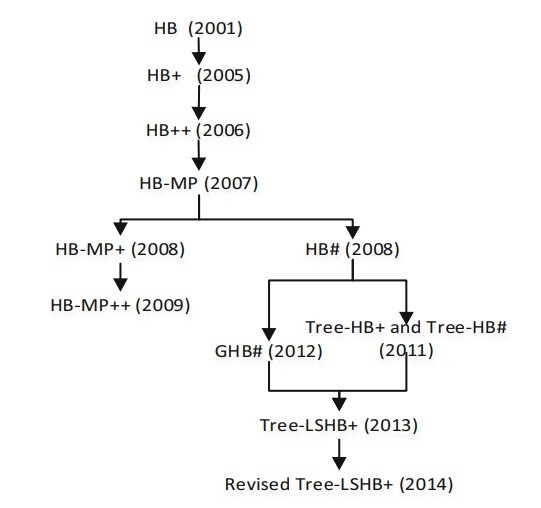
3.4 پروتکل های فوق سبک
3.5 روش های بازشناسایی جدید تر
4 ارزیابی قیاسی
5 نتیجه گیری
Abstract
1 Introduction
2 Authentication protocols
2.1 Classes of authentication protocols
2.2 Goals of authentication protocols
3 Examination and comparisons of authentication protocols
3.1 Fully fledged protocols
3.2 Simple protocols
3.3 Lightweight protocols
3.4 Ultra-lightweight protocols
3.5 Less traditional forms of authentication
4 Comparison evaluation
5 Conclusion
References
