
دانلود رایگان مقاله مجازی سازی امن برای محاسبات ابری
چکیده
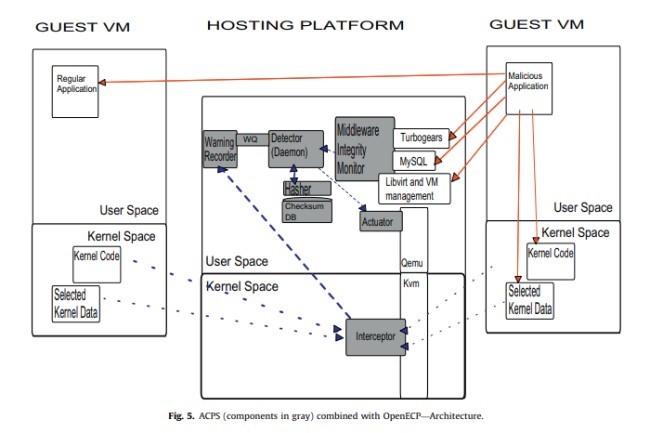
تصویب و انتشار محاسبات ابری جزء موارد امنیتی حل نشده است که ارائهدهنده و کاربران ابر را تحت تاثیر قرار میدهد. در این مقاله، نشان میدهیم که چگونه مجازیسازی میتواند با حفاظت از یکپارچگی ماشینهای مجازی مهمان و اجزای زیرساخت ابری باعث افزایش امنیت محاسبات ابری شود. به طور خاص، یک معماری جدید، سیستم پیشرفتهی حفاظت از ابر(ACPS)، را پیشنهاد میکنیم که باعث تضمین افزایش امنیت در منابع ابر میشود. ACPS میتواند بهطور موثر یکپارچگی مهمان و زیرساخت قطعات را نظارت کند، در حالی که هنوز بهطورکامل به ماشینهای مجازی و به کاربران ابر شفاف نیست. ACPS به صورت محلی میتواند به نقض امنیت به عنوان یک لایه بیشتر در مدیریت امنیت از چنین رویدادهایی واکنش نشان دهد. یک نمونه اولیه از پیشنهاد ما این است که ACPS به طور کامل در دو راهحل متن باز در حال اجرا است: Eucalyptus و OpenECP. نمونه اولیه در برابر اثربخشی و عملکرد تست شده است. بهطور خاص: (الف) اثر نمونهی آزمایش ما در برابر حملات شناخته شده نشان داده شده است؛ (ب) ارزیابی عملکرد نمونه اولیه ACPS تحت انواع مختلف از حجم کار انجام شده است. نتایج نشان میدهد که پیشنهاد ما در برابر حملات انعطاف پذیر است و سربار در مقایسه با امکانات ارائه شده کوچک است.
1. معرفی
اینترنت در کنار انقلابهای دیگراست، که در آن منابع در سطح جهان شبکه شده است و بهراحتی میتوان به اشتراک گذاشت. پردازش ابری جزء اصلی از این دیاگرام است، که یک مخزن بزرگ از اینترنت را ارائه میکند که در آن منابع برای هر کسی به عنوان سرویس در دسترس است. بهطور خاص، گرههای ابر به طور فزایندهای محبوب هستند اگرچه امنیت و حریم خصوصی مسائل حل نشده موجب کم شدن سرعت پذیرش و موفقیت آن شده است. در واقع، صداقت، محرمانه بودن و نگرانی در دسترس بودن، هنوز هم از مشکلات باز است که نیاز به پاسخ و راهحلهای کارآمد و موثر میباشد. گره ابر ذاتا به حملات اینترنتی نسبت به راهحلهای سنتی، اندازهی آنها و خدمات مربوط به پیچیدگی که به ارمغان میآورد، آسیبپذیرتر است. در واقع، ابر اینترنتی با تمام جوانب مثبت و منفی یک سیستم فراگیر است. در نتیجه، افزایش حفاظت گرههای ابر یک کار چالش برانگیز است. بنابراین به رسمیت شناختن تهدیدات برای ایجاد فرآیندهای امنیتی برای محافظت از خدمات و سیستمعاملهای میزبان حملات بسیار مهم است.
محاسبات ابری در حال حاضر از اهرم مجازیسازی برای بار تعادل از طریق تأمین پویا و مهاجرت ماشین مجازی (VM یا مهمان) در میان گرههای فیزیکی استفاده میکند. ماشینهای مجازی در اینترنت به انواع بسیاری از فعل و انفعالات که در معرض تکنولوژی مجازیسازی هستند میتواند کمک کند در حالی که فیلتر اطمینان درجه بالاتری از امنیت است. بهطور خاص، مجازیسازی میتواند به عنوان یک جزء امنیتی استفاده شود. به عنوان مثال، ارائهی نظارت بر ماشینهای مجازی، مدیریت آسان بر امنیت خوشههای پیچیده، مزارع سرور و زیرساخت محاسبات ابری. با اینحال، فنآوریهای مجازی همچنین نگرانیهای بالقوهی جدیدی را با توجه به امنیت ارائه میکنند، همانطور که در بخش 4 خواهیم دید.
مشارکتها: هدف از این مقاله،: (الف) بررسی مسائل مربوط به امنیت محاسبات ابری. (ب) ارائهی یک راهحل برای مسائل فوق.
در این مقاله مسائل مربوط به امنیت ابر و مدل، تهدیدها و شناسایی الزامات اصلی یک سیستم حفاظتی را تجزیه و تحلیل میکنیم. بهطور خاص، یک چارچوب معماری، سیستم پیشرفتهی حفاظت ابر (ACPS)، برای افزایش امنیت گره ابر ارائه میکنیم. ACPS براساس نتایج حاصل از KvmSec (لومباردی و دی پیترو، 2009) است و KvmSma (لومباردی و دی پیترو، 2010) پسوند امنیتی نمونهی اولیه از ماشین مجازی لینوکس است (KVM کومرانت، سال)، این نیز از معماری TCPS الهام گرفته است (لومباردی و دی پیترو، 2010). ACPS یک سیستم محافظت کامل برای ابرها است که بهصورت شفاف بر قطعات ابر و تعامل با منابع محلی و راه دور برای محافظت و بهبود حملات، نظارت میکند.
در زیر ما نشان دادیم که چگونه ACPS میتواند بهطور کامل مجازیسازی را به ارائه حفاظت در سیستمهای ابر مانند Eucalyptus بهکار ببرد (نورمی و همکاران، 2009) و (Openecp، 2010) و (انومالی، 2009). در واقع، OpenECP یک کد منبع به طور کامل باز است؛ که معماری و کد یکسانی را به اشتراک میگذارد. پیادهسازی نمونهی اولیه ارایه شده است. اثربخشی و عملکرد آن تست شده است. نتایج نشان میدهد که پیشنهاد ما در برابر حملات انعطاف پذیر است و سربار آن در مقایسه با ویژگیهای ارائه شده بسیار کوچک است.
یکی از نتایج اصلی تحقیق ما یک چارچوب است که یک سیستم حفاظت ابری برای پشتیبانی مجازیسازی در سراسر میزبانهای فیزیکی از طریق اینترنت را فراهم میکند.
نقشه راه. باقیماندهی این مقاله به شرح زیر است: بخش بعدی مربوط به بررسی کارهای مرتبط است. بخش 3 اطلاعات پس زمینه را فراهم میکند، در حالی که بخش 4 مسائل مربوط به امنیت ابر را طبقهبندی میکند. بخش 5 موارد مورد نیاز برای ACPS و معماری را توضیح میدهد. در بخش 6 جزئیات اجرا ارائه میشود، در حالی که اثر و عملکرد آن در بخش7 بحث شده است. در نهایت، بخش 8 برخی از نتیجهگیریها را مورد بحث قرار میدهد.
2. کارهای مرتبط
اگر چه مسائل خصوصی در رایاتش ابری توسط پیرسون شرح داده شده است (2009)، اما امنیت محیط رایانش ابری در گذشته کمتر مورد بحث قرار گرفته است. برخی از مسائل جالب امنیت در سال 2009 توسط Siebenlist بحث شده است. یک مقاله جامع در قالب بررسی جامع راهکارهای امنیت به وسیله Cachin و همکارانش ارائه شده است. یک ابر امن برای ارزیابی ریسک به تازگی توسط ENISA در سال 2009 ارائه شده است. همچنین پیشنهادی توسط Armbrust و همکارانش ارائه شده است که ارزش خواندن را دارا میباشد. این مقالات نقطه شروع کار ما شده است و ما برای تعریف مسئله و بیان مشکل و همچنین بهبود مشکلات این راهکارها به آنها رجوع کردهایم.
یک مرجع اساسی برای کار ما استفاده از کار Ristenpart در سال 2009 است. این کار نشان میدهد که برای نمونههای افزایشی ماشینهای مجازی، میتوان یک co-resident بر روی ماشین مجازی هدف یافت. پس از آنکه co-resident با موفقیت به دست آمد. حملات میتوانند به صورت تئوری اطلاعات هدف را استخراج کنند. هر مخربی ممکن است به طور متناوب نمونههای فعالی را ایجاد نماید. Ristenpart نشان میدهد که امکان اجارهی ماشینهای مجازی بیشتر برای داشتن co-resident وجود دارد و همچنین نشان میدهد که طراحی هر co-resident بسیار ساده است.
Abstract
Cloud computing adoption and diffusion are threatened by unresolved security issues that affect both the cloud provider and the cloud user. In this paper, we show how virtualization can increase the security of cloud computing, by protecting both the integrity of guest virtual machines and the cloud infrastructure components. In particular, we propose a novel architecture, Advanced Cloud Protection System (ACPS), aimed at guaranteeing increased security to cloud resources. ACPS can be deployed on several cloud solutions and can effectively monitor the integrity of guest and infrastructure components while remaining fully transparent to virtual machines and to cloud users. ACPS can locally react to security breaches as well as notify a further security management layer of such events. A prototype of our ACPS proposal is fully implemented on two current open source solutions: Eucalyptus and OpenECP. The prototype is tested against effectiveness and performance. In particular: (a) effectiveness is shown testing our prototype against attacks known in the literature; (b) performance evaluation of the ACPS prototype is carried out under different types of workload. Results show that our proposal is resilient against attacks and that the introduced overhead is small when compared to the provided features.
1. Introduction
Internet is on the edge of another revolution, where resources are globally networked and can be easily shared. Cloud computing is the main component of this paradigm, that renders the Internet a large repository where resources are available to everyone as services. In particular, cloud nodes are increasingly popular even though unresolved security and privacy issues are slowing down their adoption and success. Indeed, integrity, confidentiality, and availability concerns are still open problems that call for effective and efficient solutions. Cloud nodes are inherently more vulnerable to cyber attacks than traditional solutions, given their size and underlying service-related complexity—that brings an unprecedented exposure to third parties of services and interfaces. In fact, the cloud ‘‘is’’ the Internet, with all the pros and cons of this pervasive system. As a consequence, increased protection of cloud internetworked nodes is a challenging task. It becomes then crucial to recognize the possible threats and to establish security processes to protect services and hosting platforms from attacks.
Cloud Computing already leverages virtualization for load balancing via dynamic provisioning and migration of virtual machines (VM or guest in the following) among physical nodes. VMs on the Internet are exposed to many kinds of interactions that virtualization technology can help filtering while assuring a higher degree of security. In particular, virtualization can also be used as a security component; for instance, to provide monitoring of VMs, allowing easier management of the security of complex cluster, server farms, and cloud computing infrastructures to cite a few. However, virtualization technologies also create new potential concerns with respect to security, as we will see in Section 4.
Contributions: The goal of this paper is twofold: (a) to investigate the security issues of cloud computing; (b) to provide a solution to the above issues.
We analyzed cloud security issues and model, examined threats and identified the main requirements of a protection system. In particular, we developed an architecture framework, Advanced Cloud Protection System (ACPS), to increase the security of cloud nodes. ACPS is based on the results of KvmSec (Lombardi and Di Pietro, 2009) and KvmSma (Lombardi and Di Pietro, 2010) prototype security extensions of the Linux Kernel Virtual Machine (KVM Qumranet, year), It is also inspired by the TCPS architecture (Lombardi and Di Pietro, 2010). ACPS is a complete protection system for clouds that transparently monitors cloud components and interacts with local and remote parties to protect and to recover from attacks.
In the following we show how ACPS can leverage full virtualization to provide increased protection to actually deployed cloud systems such as Eucalyptus (Nurmi et al., 2009) and (Openecp, 2010) (also referred to as Enomalism Enomaly, 2009 in the following). In fact, OpenECP is a fully open source code fork of the previously open source Enomalism offer; as such, it shares the same architecture and codebase. A prototype implementation is presented. Its effectiveness and performance are tested. Results indicate that our proposal is resilient against attacks and that the introduced overhead is small—especially when compared to the features provided.
One main outcome of our research is a framework that allows virtualization-supported cloud protection across physical hosts over the Internet.
Roadmap. The remainder of this document is organized as follows: next section surveys related work. Section 3 provides background information, while Section 4 classifies cloud security issues. Section 5 describes ACPS requirements and architecture. In Section 6 implementation details are provided, while effectiveness and performance are discussed in Section 7. Finally, Section 8 draws some conclusions.
2. Related work
While privacy issues in clouds have been described in depth by Pearson (2009), cloud security is less discussed in the literature (Gu and Cheung, 2009). Some interesting security issues are discussed in Siebenlist (2009), while an almost complete survey of security in the context of cloud storage services is provided by Cachin et al. (2009). An exhaustive cloud security risk assessment has been recently presented by Enisa (2009). Also worth reading is the survey on cloud computing presented in Armbrust et al. (2009). These papers have been the starting points of our work and we refer to them in terms of problems and terms definition.
A fundamental reference for our research is the work on co-location (Ristenpart, 2009) by Ristenpart. This work shows that it is possible to instantiate an increasing number of guest VMs until one is placed co-resident with the target VM. Once successfully achieved co-residence, attacks can theoretically extract information from a target VM on the same machine. An attacker might also actively trigger new victim instances exploiting cloud auto-scaling systems. Ristenpart shows that it practical to hire additional VMs whose launch can produce a high chance of co-residence with the target VM. He also shows that determining co-residence is quite simple.
چکیده
1. معرفی
2. کارهای مرتبط
3. پیش زمینه
4. مسائل امنیتی ابر
5. سیستم پیشرفتهی محافظت از ابر
5.1. مدل تهدید
5.2. نیازمندیها
5.3. روش ارائه شده
6. اجرا
7. اثربخشی-ACPS مورد حمله
7.1. آناتومی از حمله و واکنش
7.2. کارآیی
8. نتیجهگیری
منابع
Abstract
1. Introduction
2. Related work
3. Background
4. Cloud security issues
4.1. Cloud security model
5. Advanced cloud protection system
5.1. Threat model
5.2. Requirements
5.3. Proposed approach
6. Implementation
7. Effectiveness—ACPS under attack
7.1. Anatomy of attack and reaction
7.2. Performance
8. Conclusion
References
