
دانلود رایگان مقاله تجزیه و تحلیل امنیت مبتنی بر تهدید برای اینترنت اشیا
چکیده
اینترنت اشیاء (IoT) یک پارادایم در حال ظهور است که بر اتصال درونی اشیاء یا وسایل با یکدیگر یا و کاربران تمرکز دارد. پیش بینی می شود که این فناوری نقطه عطفی در توسعه خانه ها و شهرهای هوشمند گردد. موفقیت و دستیابی به استفاده فراگیر برای هر فناوری مستلزم جلب اعتماد کاربران از طریق فراهم آوردن امنیت کافی و تضمین حریم خصوصی است. با وجود علاقه رو به رشد جامعه پژوهش به IoT و ظهور مطالعات و مقالات متعددی در خصوص معماری و عناصر آن؛ همچنان جای خالی تحلیلی جامع از ویژگیهای امنتیی و حریم خصوصی مورد نیاز یک سیستم که دستگاههای تشکیل دهنده آن از قابلیتهای متفاوتی برخوردارند احساس میشود. در این مقاله یک مدل تهدید مبتنی بر یوزکیس های (use-case) اینترنت اشیاء را ارائه می دهیم. که میتواند در تعیین چگونگی صرف (سرمایهگذاری) تلاشها به منظور ایجاد امنیت در این سیستمها مورد استفاده قرار گیرد. پایان کار را با ارائه پیشنهاد شاخصهایی که میتوانند در استفاده از اینترنت اشیاء امنیت و تضمین حریم خصوصی را فراهم آورند جمع بندی خواهیم نمود.
1. مقدمه
در سال های اخیر جهان با پیشرفت تکنولوژی سریعی روبرو گشته است که هر یک تاثیر قابل توجهی در زندگی روزمره دارد. ظهور فن آوری هایی همچون گوشی های هوشمند؛ تبلت ها؛ لپ تاپ ها و رایانه های شخصی در طول زمان و در بعد فاصله ای موجب افزایش ارتباط متقابل شده است. فن آوری معاصر فراتر از تقویت ارتباط بین انسان ها است و در حال حاضر برای دستیابی به یک هدف مشترک ارتباط بین انسان ها و اشیاء و در واقع ارتباط اشیاء با یکدیگر را تسهیل می کند؛ این تعریف اینترنت اشیاء (IoT) نامیده می شود. اعتقاد بر این است که اینترنت اشیاء نقطه عطفی در تحول تکنولوژی جهان است که در کمتر از 6 سال گذشته دارای نرخ توسعه 270 درصدی بیشتر از دستگاه های موبایل بوده است. طبق این پیش بینی بسیاری از دولت ها و شرکت های بزرگ بودجه قابل توجهی برای تحقیقات روی موضوع اینترنت اشیاء اختصاص داده اند.
اینترنت اشیاء نقشی اساسی در شکل دهی به آینده شهرهای هوشمند ایفا می کند. از دیدگاه کاربر شخصی؛ اینترنت اشیاء خود را در کاربرد ابزارهای داخلی در محل کار آشکار می کند به عنوان مثال سیستم هایی همچون ترموستات هوشمند؛ ماشین های هوشمند و جامعه هوشمند. علاوه بر این؛ با توجه به محیط های شرکتی اینترنت اشیاء قادر به خودکار سازی کارها؛ ارائه محیط های هوشمند تر برای کارمندان و مدیریت مصرف انرژی با هدف کاهش هزینه ها خواهد بود. اینترنت اشیاء با استفاده از تکنولوژی های دیگر مانند سنسورها؛ شناسه های فرکانسی رادیو (RFIDs)؛ محرک ها و مترهای هوشمند می تواند به اهداف فوق الذکر دست یابد. این دستگاه ها برای ایجاد یک رفتار جدید که هر شی برای دستیابی به قابلیت مورد نظر کمک می کنند به یکدیگر لینک می شوند. یک مثال قابل توجه از چنین کاربردی یک سیستم ترموستات است که دما را حس می کند و خود را با یادگیری الگوهای رفتاری کاربران خود تنظیم می کند.
واجب است که همه جنبه های امنیت و حریم خصوصی به طور کامل در نظر گرفته شود. در واقع رسیدگی به چنین حقایقی ضمن یک چالش از همه ضروری تر است. از آنجایی که اینترنت اشیاء ملقمه ای از فن اوری های بزرگ فردی است بسیاری از آنها ممکن است با توجه به حریم خصوصی و امنیت نقص هایی داشته باشند؛ در صورت عدم استطاعت توجه کافی به موضوع این مقاله ممکن است اینترنت اشیاء به شیوه ای تهدید آمیز و نادرست ابزار سازی شود.
ماهیت پیچیده امنیت در اینترنت اشیاء حول محور این حقیقت است که ؛ با این حال که ارتباط چندین فن اوری به یکدیگر یک چالش بزرگ است اما سیستم تلاش می کند که دستگاه های محدود به محاسبات؛ انرژي و ذخیره سازی را به صورت ایمن با یکدیگر مرتبط کند. برخی از دستگاه های استفاده شده توسط اینترنت اشیاء تنها می توانند مکانیزم های بسیار اساسی امنیتی را تطبیق دهند و نظیر هریک ناتوان از حفظ یکپارچگی و محرمانگی اطلاعات کابران است. علاوه بر این دستگاه هایی همچون سنسورها و RFID ها فاقد یک رابط کاربری ساده مانند یک کلید خاموش/روشن یا نشانگر وضعیت است بنابراین هنگامی که مردم به این دستگاه ها اعتماد می کنند یک محدودیت روانی بصری برای آن ها به وجود می آید. امروزه نگرانی های حریم خصوصی تبدیل به یک مانع شده است و پیشرفت بسیاری از فن آوری ها را کاهش می دهد.
به تازگی بسیاری از فن اوری ها برای حفظ امنیت کافی و مکانیزم های حریم خصوصی با شکست مواجه شده اند و در نتیجه موجب آزردگی بسیاری از افرادگشته اند. در اینترنت اشیاء برای جلب اعتماد عموم باید تضمین کرد که برای امنیت و حریم شخصی این سیستم ها چنین مشکلاتی به وجود نخواهد آمد.
در این مقاله اینترنت اشیاء را از دیدگاه موارد استفاده use- cases مورد بحث قرار می دهیم. بخش های بعدی یک دید کلی از کارهای انجام شده در این زمینه را ارائه می دهد؛ بخش 3 چندین سناریو جالب که مربوط به دنیای امروز است را به طور مفصل بیان می کند؛ بخش 4 یک مدل تهدید را مورد بحث قرار می دهد؛ بخش5 تجزیه و تحلیل امنیتی را بر اساس این یوزکیس ها به دستگاه های اینترنت اشیاء ارائه می دهد؛ بخش 6 ویژگی های مطلوب امنیتی و شخصی را در سیستم های اینترنت اشیاء فهرست می کند و درنهایت در بخش 7 به کارهایی که در آینده در این زمینه برنامه ریزی کرده ایم نگاهی اجمالی خواهیم داشت. به طور ویژه برنامه اصلی ما به این صورت است:
- تعریف چندین یوزکیس برای اینترنت اشیاء.
- ایجاد مدل سازی تهدید ب عنوان روشی برای تجزیه و تحلیل موارد استفاده تعریف شده.
- فرموله کردن مجموعه ای از ویژگی های امنیتی و خصوصی مطلوب برای اینترنت اشیاء
2. کارهای مرتبط
با توجه به علاقه روزافزون به اینترنت اشیاء نشریات متعددی در امنیت و حریم خصوصی در این زمینه وجود دارد. در حال حاضر هزاران تعریف از چشم انداز اینترنت اشیاء؛ برنامه های کاربردی و فن آوری ها وجود دارد که به طور خلاصه برخی از جنبه های امنیتی و شخصی را مورد خطاب قرار می دهد.آتزوری و همکاران اهمیت امنیت در زمینه اینترنت اشیاء را مورد بحث قرار داده اند و بر جنبه های امنیت عناصر تمرکز دارند. در این مطالعه اشاره شد که به علت محدودیت دستگاه های ساخته شده اینترنت اشیاء و ویژگی های پروتوکل های ارتباطی جاری؛ اعمال مکانیزم های امنیتی پیچیده بسیار چالش برانگیز است. برخی از دستگاه ها ممکن است قادر به کنترل دسترسی برای کاربران مختلف؛ طرح تصدیق پشتیبانی کافی یا حتی استفاده از کانال های ارتباطی امن بین دستگاه ها نباشند. با این حال به خاطر داشته باشید که اقدامات امنیتی مورد نیاز وابسته به کاربرد است. برای مثال در Near Field Communication (NFC) مجاورت فیزیکی برای ایجاد ارتباط بسیار حیاتی است که این فن آوری را برای کاربردهای مختلف مفید می سازد. بنابراین به علت این ویژگی برخی از برنامه ها که از NFC استفاده می کنند ممکن است نیازمند طرح امنیتی پیچیده ای مانند کانال رمزگذاری شده نباشند. برای مثال در برخی موارد ممکن است کاربران به دیگر کاربرانی که ردوبدل اطلاعات در حضور انها مشاهده می شود توجه نکنند. برای مثال در یک کاربرد داخلی برای اینترنت اشیاء برای جلوگیری کودکان از تماشای تلویزیون بدون نظارت بزرگسالان؛ ممکن است کاربر نیازمند پروتکل های ارتباطی پیچیده نباشد و تنها استفاده از مکانیزم های کنترل دسترسی برای دسترسی به دستگاه یا رمزنگاری متقارن به جای رمزنگاری نامتقارن برای برقراری ارتباط کافی باشد.
اینترنت اشیاء با توجه به ماهیت ناهمگن خود با چالش های امنیتی و حریم خصوصی متعددی مواجه می شود. گروه های تحقیقاتی مختلف قانون های مختلفی را برای پرداختن به این مسائل در نظر گرفته اند. رومان و همکاران فن آوری های متعددی را در زمینه اینترنت اشیاء ارائه کرده اند؛ فن آوری های جاری و امکان پذیری آنها برخی از دستگاه های اینترنت اشیاء را مورد بحث قرار داده اند و مجموعه ای از نیازمندی های امنیتی را برای دستگاه های اینترنت اشیاء ارائه کرده اند. همان گروه در مطالعه بعدی معماری متمرکز و توزیع شده اینترنت اشیاء و و پیامد آنها بر جنبه های امنیتی را مقایسه کرده اند. علاوه بر این کازلاو و همکاران تهدید های امنیتی و حریم شخصی را در معماری اینترنت اشیاء برای تحلیل تهدیدها در سطوح مختلف معماری با استفاده از یک رویکرد سیستماتیک مورد بحث قرار داده اند.
Abstract
The Internet of Things (IoT) is an emerging paradigm focusing on the inter-connection of things or devices to each other and to the users. This technology is anticipated to become an integral milestone in the development of smart homes and smart cities. For any technology to be successful and achieve widespread use, it needs to gain the trust of users by providing adequate security and privacy assurance. Despite the growing interest of the research community in IoT, and the emergence of several surveys and papers addressing its architecture and its elements, we are still lacking a thorough analysis of the security and privacy properties that are required for a system where the constituent devices vary in their capabilities. In this paper we provide a threat model based on use-cases of IoT, which can be used to determine where efforts should be invested in order to secure these systems. We conclude by recommending measures that will help in providing security and assuring privacy when using IoT.
I. INTRODUCTION
In the last few years the world has experienced rapid advancement in technology, the likes of which has had a significant impact on our daily lives. The rise of technologies - smartphones, tablets, laptops and PCs - has engendered an increase in interconnectedness through time and across the spatial dimension. Contemporary technology has moved beyond fostering only connections between humans, and now facilitates both the linkage of people to things and indeed, things to one another, to achieve a common goal; this being termed The Internet of Things (IoT). IoT is believed to be the next milestone in the technological evolution of the world, it having an expansion rate 270 percent higher than mobile devices in less than six years [1]. Based on this prediction, many governments and large corporations have earmarked substantial funding for research on IoT.
IoT is going to have a substantial role in shaping the future of smart cities. From the private user’s perspective it manifests itself in the application of domestic tools at work; for example, systems such as the smart thermostat, smart car, and smart community. Moreover, with regard to the corporate environment, IoT will enable automation of work, the provision of smarter environments for employees, and the management of power consumption with the aim of reducing expenses [2]. IoT is able to achieve the aforementioned through utilisation of other technologies [3], [4] - for instance, sensors, Radio Frequency IDentifiers (RFIDs), actuators, and smart meters. These devices are linked together to create a new emergent behaviour where each thing contributes to achieving the desired functionality. A particularly salient example of such an application is a thermostat system that senses the temperature and adjusts itself by learning the behaviour patterns of its users [5].
The value of IoT could not possibly be overestimated, however it is obligatory that a thorough consideration be given to all aspects of security and privacy. Indeed, tackling such facts, whilst a challenge, is all the more imperative. As IoT, being the amalgam of a great many individual technologies, many of which may well have flaws with respect to security and privacy, could conceivably be instrumentalised in a sinister and far more threatening manner if there is a failure to afford sufficient attention to the subject matter of this paper.
The complex nature of security in IoT revolves around the fact that, while in itself connecting several technologies together is a great challenge, the system attempts to securely connect devices that are limited in computation, power, and storage. Some of the devices used by IoT can accommodate only very basic security mechanisms, the likes of which are incapable of maintaining the integrity and confidentiality of the users’ data. Moreover, these devices - for instance, sensors, and RFIDs - lack a simple user interface, like an ON/OFF button or status indicator, thus presenting a visual psychological limitation for people when it comes to trusting these devices.
Nowadays, privacy concerns have become a hurdle; slowing the advancement of many technologies[6]. Furthermore, it has been shown that trust in a technology diminishes when the latter slanders or exposes the individual [7], [8], [9], and, recently, many technologies have failed to provide adequate security and privacy mechanisms, thereby causing pain and suffering to those afflicted [10]. In order to gain the trust of the public in the Internet of Things, we need to ensure the same failures with respect to privacy and security do not come to pass with this system, by ensuring the appropriate mechanisms to guarantee such things exist from the onset.
In this paper, we discuss the Internet of Things from a use-cases perspective. The following section provides a general overview of the work done in the field; section 3 details several interesting scenarios which are relevant to today’s world; section 4 discusses a threat model; section 5 provides a security analysis to the IoT devices based on these use-cases respectively; section 6 lists security and privacy properties desirable in IoT systems; whilst finally, in section 7 we give a glimpse of the future work we plan to do in this field. In particular, our main contributions are:
• Defining several use-cases for the Internet of Things.
• Establishing threat modelling as a method for analysing the use-cases defined.
• Formulating a set of desirable security and privacy properties for IoT.
II. RELATED WORK
Due to the rising interest in the Internet of Things, there have been numerous publications on security and privacy in this context. There are currently a myriad of descriptions of IoT visions, applications, and enabling technologies [11], [12], [13], [14] that briefly address some security and privacy aspects. Atzori et al. [11] has discussed the importance of security in IoT context and focused on the security aspects of the elements. In this survey it was pointed out that due to the limitation of the devices composing the IoT, and the properties of the current communication protocols, it is very challenging to employ complex security mechanisms. Some devices might not be able to have access control for different users, support sufficient authentication schemes, or even use secure communication channels between devices. However, it is important to keep in mind that the required security measures are application dependent. For instance, in Near Field Communication (NFC), physical proximity is vital for establishing the connection, which makes this technology useful for various applications. Therefore, due to this property, some applications using NFC might not require a complex security scheme such as encrypted channel. For example, in some instances the users might not care about other people seeing the exchanged data in their presence. For instance, in a domestic use for IoT, in order to prevent children from watching TV without adult supervision, the user might not need complex communication protocols and it would suffice to only use access control mechanisms to access the device, or symmetric encryption rather than asymmetric for communication.
Due to its heterogeneous nature, the Internet of Things poses many security and privacy challenges[15]. Different research groups have adopted diverse directions for addressing these issues. Roman et al. [16] presented several technologies in IoT context, discussed current technologies and their feasibility for some IoT devices, and provided a set of security requirements for IoT devices. In a subsequent study, the same group [17] compared the centralised and distributed architecture of IoT and their implication on security aspects. Moreover, Kozlov et al. [18] discussed security and privacy threats in IoT architecture, using a systematic approach to analyse the threats at different levels of the architecture.
چکیده
1. مقدمه
2. کارهای مرتبط
3. یوزکیس های اینترنت اشیاء
A. مدیریت انرژي
B. ماشین هوشمند
C. سیستم بهداشت و درمان هوشمند
4. مدل تهدید
A. منابع تهدید
B. کلاس های بردارهای حملات
5. اثر حمله
A. محرک ها
B. سنسورها
C. تگ های RFID
D. شبکه، NFC و اینترنت
6. ویژگی های امنیت مطلوب و حریم خصوصی
A. ویژگی های امنیت
محرک ها، سنسورها و RFID ها
اینترنت، شبکه و NFC
محرک ها، سنسورها، RFID ها، شبکه
B. ویژگی های حریم خصوصی
7. کار آینده
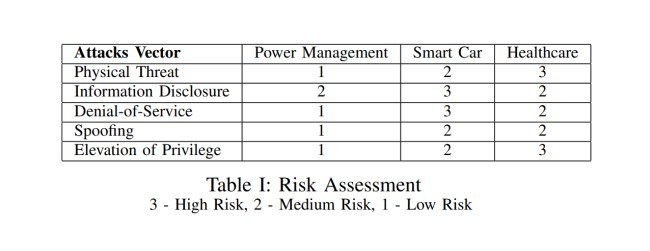
A. ارزیابی ریسک مقدماتی
8. نتیجه گیری
منابع
Abstract
1. INTRODUCTION
2. RELATED WORK
3. INTERNET OF THINGS USE-CASES
A. Power Management
B. Smart Car
C. Smart Healthcare System
4. THREAT MODEL
A. Sources of Threats
B. Classes of Attacks Vectors
5. ATTACKS IMPACT
A. Actuators
B. Sensors
C. RFID tags
D. Network,NFC and the Internet
6. DESIRABLE SECURITY AND PRIVACY PROPERTIES
A. Security Properties
Actuators, Sensors, and RFIDs
Internet,Network, and NFC
Actuators, Sensors, RFIDs, Network
B. Privacy Properties
7. FUTURE WORK
A. Preliminary Risk Assessment
8. CONCLUSION
REFERENCES
