
دانلود رایگان مقاله مدیریت هویت و حفاظت از تمامیت در اینترنت اشیاء
چکیده
احراز هویت و مدیریت هویت به حفاظت از منابع و توجیه کردن اعتماد به عملیات اصلی توسط مشتری سرویس و فراهم کننده ی سرویس کمک می کند. بعلاوه، مدیریت هویت می تواند سخت افزار کمک کننده به حفظت از تمامیت را پشتیبانی کند. در اینترنت اشیاء (IOT)، تعداد بالای دستگاه های سبگ وزن نیازمند راه حل های مقیاس پذیر و سبک وزن برای اطمینان به مدیریت است. مقاله چارچوبی برای احراز هویت و حفاظت از تمامیت مناسب برای یک محیط IOT ارائه می دهد.
1. دیباچه
عبارت "اینرنت اشیاء" به یک قرارداد در دنیا که "همه چیز" به صورت منحصر به فرد از طریق نوعی دستگاه ارتباطی قابل شناسایی و نشانی پذیر هستند و بتوان اشیاء را برای هدف های مختلف موقعیت یابی کرد، به کار گرفت،حفظ و نگهداری کرد و مورد بازرسی قرار داد.
"اشیاء" چه به عنوان ارزش مادی یا چه در حالت سویسی که رائه می دهند، منابع ارزشمندی هستند (ارائه می کنند). منابع نیاز دارند تا از طریق چرخه ی زندگیشان مدیریت شوند، و دسترسی به منابع نیاز دارند تا کنترل و حسابرسی شوند. هویت منابع و مشتری هایشان (در جایی که قابل اطلاق باشد) باید توسط یک سیستم مدیریت هویت مدیریت، محافظت و نگهداری شود، و باید مکانیزم هایی در محل برای احراز هویت ها، کنترل دسترسی به منابع و حفاظت از کاربرد اطلاعات به خاطر حفاظت از حریم خصوصی وجود داشته باشد (1).
در حوزه ی مدیریت هویت (IDM)، مفهوم تضمین هویت به عنوان یک وسیله ی مهم برای کنترل منبع در نظر گرفته شده است. یک IDM سرویس هایی برای احراز هویت که به معنی نوعی مکانیزم برای تشخیص ماهیت (به عنوان مثال یک شخص) که بر روی منبع فعالیت می کند، است ارائه می کند. احراز هویت یک شیء لزوما به معنی اطمینان از هویت نیست بلکه اطمینان از اصالت یا تمامیت آن است. احراز هویت پیش نیازی برای حسابرسی ، حسابداری و کنترل دسترسی همانند پرونده های کاربری شخصی و دیگر سرویس های نامرتبط به امنیت و مسئولیت است.
قوانین IDM به خوبی درک شده اند اما سیستم های IDM پیچیده هستند و اکثرا در محیط های نسبتا همگنی یافت می شوند که استانداردهای فراگیر برای ارائه ی اطلاعات و پروتوکل های شبکه بتوانند اجرا شوند. اینترنت اشیاء مشخصاتی ذاتی دارد که برای گسترش یک IDM چالش هایی ارائه می کند:
• مقیاس مطلق سیستم، به صورت بالقوه میلیارد ها شیء با چرخه ی زندگی کوتاه و "نرخ تولد" بالا
• عدم تجانس واحد ها، که از چیپ های RFID با حداقل توان پردازش، قابلیت های ارتباطی و حافظه ی داخلی تا کامپیوتر های مقیاس بزرگ با منابع زیاد تغییر می کند. هیچ استاندارد رایجی برای ارائه یا اانتقال بر روی این محدوده ی تجهیزات نمی تواند اجرا شود و چندین استاندارد مختلف به احتمال زیاد همزیستی می کنند.
• تعداد بالای حوزه های مدیریت. دستگاه های IOT توسط اجتماع بزرگی ار فراهم کننده های سرویس ها و سرمایه گذاران مدیریت و به کار گرفته می شوند. آنها به احتمال زیاد سیاست های نمگذاری بسیار مختلف ، چارچوب های امنیتی، نیازمندی های پروتوکلی و کنترل های دسترسی را به کار می برند. به منظور اتصال دادن این تفاوت ها، ممکن است که نقاط درگاهی سنتی نیاز به جایگزینی توسط پردازنده های معنا شناختی داشته باشند.
در ادامه ی مقاله، برخی مسائل و اهداف تحقیق مرتبط با IdM در اینترنت اشیاء بحث خواهد شد. مجموعه ای از مکانیزم های ارائه شده برای کنترل اصالت ارائه خواهد شد مشخصات ضروری مکانیزم ها، سادگی، احتیاط و وفق پذیریشان خواهد بود.
2. مشخصات ضروری سیستم
انتظار می رود تا اینترنت اشیاء به مقیاسی که قبلا هرگز مشاهده نشده و با محدوده ی گسترده تری از تجهیزات با منابع و توانایی مختلف بیشتر دست یابد. بعلاوه، قطعا کاربردهای آینده ی IOT به صورت شگفتی می آیند و نگاه کنونی ما بر اینکه چطور دستگاه های IOT می توانند به ساخت تجارت کمک کنند را به چالش می کشد.
بنابراین، گسترش تکنولوژی برای اهداف IOT باید قوانین شناخته شده از محاسبه ی مقیاس بزرگ را دنبال کند (2).
A. گرایش خدمت
ممکن است که "اشیاء" به شکل اهداف خنثی به نظر برسند اما ممکن است که به عنوان فراهم کننده های سرویس به خوبی در نظر گرفته شوند. ساده ترین سرویس ممکن، معلوم کردن هویت یک فرد است که حتی یک دستگاه ساده ی RFID قادر به انجام دادن آن است. بنابراین قرار دادن اینترنت اشیاء در چشم انداز جهت دار سرویس که در آن تمام تراکنش ها یک آغازگر و یک پاسخ دهنده دارند، مفید است.
اتصال سست میان مشتری و سرویس، و جدایی واضح خط اتصال از پیاده سازی، شانس های قابلیت همکاری بین اشیاء در آینده را افزایش می دهد.
B. مدیریت هویت
رمزنگاری ساده است اما مدیریت کلمه ی عبور سخت است. اکثر مکانیزم های امنیتی به برخی الگوریتم های رمزی متکی هستند، و همه ی آنها از مواد کلمه ی عبور گذاری که باید به طور ایمن در بخش ها مستقر شوند، استفاده می کنند. مدیریت کلمه ی عبور شامل تولید، گسترش، به روز رسانی و برداشت کلمه ی عبور وکمک به کلمه ی عبور ها توسط هویت ها به روشی که بتواند توسط هر کسی تایید شود، می شود . همچنین مدیریت هویت، ویژگی مدیریت را به شکل مشخصاتی که به روشی معتبر، به صورتی ایمن به هویتی مقید هستند ارائه می کند.
Abstract
Authentication and Identity Management help to protect resources and justify trust in “bona fide” operation by service client and service provider. Besides, identity management can support hardware assisted integrity protection. In the Internet of Things (IoT), the high number of lightweight devices requires scalable and lightweight solutions to trust management. The paper proposes a framework for authentication and integrity protection well suited for an IoT environment.
I. INTRODUCTION
The expression “Internet of Things” (IoT) refers to an arrangement of the world where ”everything” is uniquely identifiable and addressable through some kind of communication device, and where things can be located, employed, maintained and inspected for different purposes.
“Things” are, or represent, valuable resources, either as material value, or in the form of the service they offer. Resources need to be managed throughout their lifecycle, and access to resources need to be controlled and audited. The identity of resources and their clients (where applicable) should be managed, protected and maintained by an identity management system, and there must be mechanisms in place for authentication of identities, access control to the resources and protection of usage data for the sake of privacy protection.[1]
In the area of Identity Management (IdM), the concept of identity assurance is considered as an important tool for resource control. An IdM offers services for authentication, which means some kind of mechanism to identify the entity (e.g. a person) which operates on a resource. Authentication of a Thing does not necessarily mean assurance of identity, but rather assurance of its genuineness or integrity. Authentication is a prerequisite for auditing, accounting and access control, as well as personal application profiles and other services not related to security or accountability.
The principles of IdM are well understood, but IdM systems are complex and mostly found in relatively homogeneous environments where pervasive standards for information representation and network protocols can be enforced. The Internet of Things have inherent properties which represent challenges to the deployment of an IdM:
• The sheer scale of the system, potentially billions of things with short life cycle and high “birth rate”.
• The heterogeneity of units, ranging from RFID chips with a minimum of processing power, communication capabilities and internal memory, to large scale computers with plenty of resources. No common standard for representation or transportation can be enforced on this range of equipment and several different standards are likely to co-exist.
• A high number of management domains. IoT devices will be managed and operated by a large community of enterprises and service providers. They are likely to employ vastly different naming policies, security frameworks, protocol requirements and access controls. In order to bridge these differences, traditional gateway nodes may need to be replaced by semantic processors.
In the rest of this position paper, some problems and research objectives related to IdM in the Internet of Things will be discussed. A set of proposed mechanisms for control of genuineness will be presented. Essential properties of the mechanisms will be their simplicity, prudence and adaptability.
II. NECESSARY SYSTEM PROPERTIES
The Internet of Things is expected to reach a scale which has never been observed before, and with a wider range of equipment with greatly different resources and capabilities. Besides, the future applications of IoT will surely come as surprises and will challenge our present view on how the IoT devices could collaborate to make business.
Therefore, the deployment of technology for IoT purposes should follow well known principles from large scale computing[2]:
A. Service Orientation
”Things” may look like passive objects, but may well be regarded as service providers. The simplest possible service is to reveal one’s identity, which even a simple RFID device is able to do. It is therefore useful to put the Internet of Things into a Service Oriented perspective, in which all transactions have an initiator and a responder.
The loose coupling between client and service, and the clear separation of interface from implementation increase the chances for future interoperability between things.
B. Identity Management
Cryptography is easy, but key management is hard. Most security mechanisms relies on some crypto algorithms, and they all employ keying material which must be deployed securely in the parties. Key management involves key generation, deployment, updating and removal, and to associate the keys with identities in a way that can be validated by everyone. Identity management also offers attribute management, in the form of properties securely bound to an identity in a validatable way.
چکیده
1. دیباچه
2. مشخصات ضروری سیستم
A. گرایش خدمت
B. مدیریت هویت
3. احراز هویت و اینترنت اشیاء
A. احراز هویت ضدرشوه
B. مدیریت هویت بدون لیست های ابطال
4. اطمینان از طریق گواهی اصالت
A. مدول پلتفرم مورد اعتماد
B. واحدهای محافظت ساده
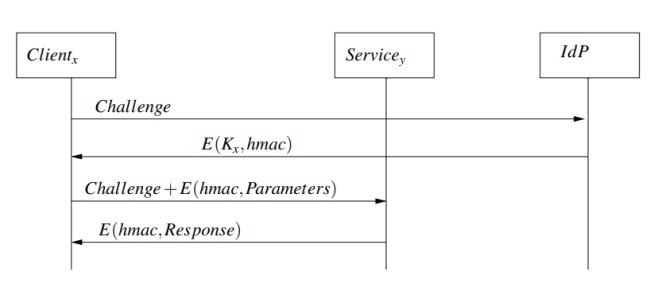
C. پروتوکل ها برای تایید اصالت
D. کنترل دسترسی
5. تحقیق مرتبط
6. نتایج
منابع
Abstract
1. INTRODUCTION
2. NECESSARY SYSTEM PROPERTIES
A. Service Orientation
B. Identity Management
3. AUTHENTICATION AND THE INTERNET OF THINGS
A. Tamperproof authentication
B. Identity management without revocation lists
4. TRUST THROUGH ATTESTED GENUINENESS
A. Trusted Platform Module
B. Simple protection units
C. Protocols for attestation of genuineness
D. Access control
5. RELATED RESEARCH
6. CONCLUSION
REFERENCES
