
دانلود رایگان مقاله رویکردی جدید برای کاهش دادن حمله حفره خاکستری در MANET
چکیده
شبکه ادهاک سیار (MANET) به عنوان دسته ای از شبکه های بی سیم تعریف می شود که قادر به عملیات بدون هرگونه زیرساخت ثابت شده است. فرضیه ی اصلی در نظر گرفته شده در این شبکه این است که همه ی گره ها، گره هایی مورد اطمینان هستند، اما در سناریوی واقعی، برخی گره ها می توانند مخرب باشند و از این رو می توانند بسته های داده را به جای انتقال به گره مقصد، به صورت انتخابی کنار بگذارند. این گره های مخرب در طول مرحله ی شناسایی مسیر عادی رفتار می کنند و بعد از آن بخشی از بسته های داده ی مسیر دهی شده از میان آنها را کنار می گذارند. چنین نوعی از حمله به عنوان حمله ی حفره ی خاکستری هوشمند شناخته می شود که نوعی موارد متوالی تشکیل دهنده ی حمله ی حفره ی خاکستری است. در این مقاله، حمله ی حفره ی خاکستری را اجرا و برای کاهش اثر آن مکانیزمی جدید مطرح کرده ایم. مکانیزم کاهش حمله ی حفره ی خاکستری (MGAM) چندین گره خاص که گره های G-IDS (سیستم شناسایی نفوذ حفره ی خاکستری) نامیده می شوند را استفاده می کند. گره های G-IDS برای شناسایی و جلوگیری از حمله ی حفره ی خاکستری در MANET به کار برده می شوند. گره های G-IDS انتقال گره های همسایگی خود را استراق سمع کرده و در زمانی که شناسایی می کند که گره، بسته های داده را کنار می گذارد، پیام هشدار را در شبکه مخابره می کند تا شبکه را درمورد هویت گره مخرب آگاه کند. لازم به ذکر است که کنار گذاری بسته های داده در گره، بزرگتر از مقدار آستانه است. سپس گره مخرب شناسایی شده بوسیله ی کنار گذاری بسته ی درخواست و پاسخ از مشارکت های بعدی اش منع می شود. شبیه ساز NS-2.35به منظور اعتبار سنجی کارآمدی مکانیزم پیشنهادی ما، استفاده می شود. نتایج شبیه سازی نشان می دهد که مکانیزم پیشنهادی در مقایسه با طرح حمله ی حفره ی خاکستری هوشمند موجود نسبتا خوب عمل می کند.
1. مقدمه
شبکه ادهاک متحرک (MANET)، یک فناوری در حال پیشرفت و فراگیرترین فناوری در میان شبکه های بی سیم است که به عنوان شبکه ی کم زیرساخت شناخته می شود. این شبکه از نوع خود تنظیم، موقت و مقیاس پذیر شبکه ها است. این نوع از شبکه ها برای عملیات های مهمی مانند میدان نبرد، عملیات نجات اضطراری و غیره مناسب است. در این نوع از شیکه، هر دستگاه نه تنها به عنوان یک میزبان بلکه به عنوان یک راهبر نیز عمل می کند. این پروتوکل های مسیریابی مانند بردار فاصله برحسب درخواست در شبکه اد هاک (AODV)، مسیریابی منبع پویا (DSR) و غیره که برای ارتباطات استفاده می شوند، بر مبنای این فرض هستند که همه ی گره ها تعاونی و قابل اعتماد هستند. بنابراین، پروتوکل های مسیریابی MANET به شدت نسبت به مدل های مختلف حمله های خودداری از خدمت (DOS)، خصوصا حمله ی کنار گذاری بسته، آسیب پذیر هستند. حمله ی کنار گذاری بسته می تواند به عنوان حمله ی کنارگذاری بسته ی کامل و کنارگذاری بسته ی جزیی دسته بندی شوند. حمله ی کنار گذاری بسته ی کامل به عنوان حمله ی حفره ی خاکستری شناخته می شود. در هنگام حمله ی کنارگذاری بسته ی کامل، گره مخرب در روند شناسایی مسیر شرکت نمی کند و سعی می کند تا ترافیک داده را از طریق دادن اطلاعات مسیر یابی غلط جذب کند و همه ی بسته های داده ی رسیده را با این کار کنار می گذارد، در حالیکه در هنگام حمله ی کنار گذاری بسته ی جزیی، گره مخرب حقیقتا در روند شناسایی مسیر شرکت می کند و همچنین بسته ی پاسخ حقیقی دریافت شده از مقصد را ارسال می کند. وقتی گره منبع بسته های داده را از طریق مسیری که شامل گره حفره ی خاکستری است، ارسال می کند، برخی از بسته های داده را کنار می گذارد و عملکرد شبکه اندکی کاهش می یابد. بنابراین، تامین امنیت در شبکه ی تک کاره در جهت اداره کردن حمله ها ضروری است. در این مقاله، مکانیزم جدیدی به عنوان مکانیزم کاهش حمله ی حفره ی خاکستری (MGAM) در جهت کاهش تاثیر حمله ی حفره ی خاکستری هوشمند در شبکه مطرح کرده ایم . می توان اذعان کرد که این طرح، مشارکت اصلی این مقاله است.
باقی مانده ی مقاله به صورت پیش رو بنا شده است. بخش 2 انواع مختلف حمله ی حفره ی خاکستری و فرایندهای راه اندازی حمله ی حفره ی خاکستری هوشمند را تشریح می کند. در بخش 3، درباره ی طرح های مختلف موجود برای اداره کردن حمله ی حفره ی خاکستری در MANET توضیح داده ایم. در بخش 4، مکانیزم در حال کارِ روش علمیِ مطرح شده را به تفصیل تشریح کرده ایم. بخش 5 در باره ی پارامترها و تحلیل های عملی در NS-2 بحث می کند. در بخش 6، مقایسه ی عملکرد رویکرد ما با ABM نشان داده می شود. مزایا و نقص های رویکرد ارائه شده و نتیجه گیری به ترتیب در بخش 7 و 8 بحث می شوند.
2. حمله حفره خاکستری
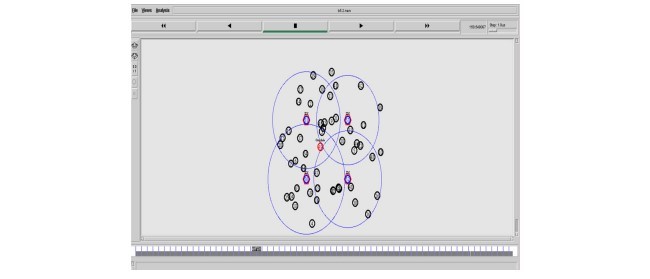
حمله حفره خاکستری یا حمله ارسال انتخابی یک حمله خودداری از خدمات است که نوعی از حمله ی سیاه چاله می باشد. در حمله ی سیاه چاله، در ابتدا، گره به عنوان یک مخرب ظاهر نمی شود اما بعدها تبدیل به یک گره مخرب می شود و بسته های داده ی انتخابی را کنار می گذارد. همان طور که در شکل 1 نشان داده شده، دو نوع از حمله های حفره ی خاکستری در MANET امکان پذیر است. اولین نوع از حمله ی حفره ی خاکستری، شماره دنباله ی تشکیل دهنده ی حمله ی حفره ی خاکستری است که در (10) نشان داده شده است. در این نوع از حمله ی حفره ی خاکستری، گره بوسیله ی ارسال شماره دنباله ی مقصد بالا با تعداد هاپ کمینه به گره منبع، پاسخ مسیر غلط می دهد. گره منبعِ دریافت کننده ی بسته های پاسخ، شروع به ارسال بسته های داده از مسیر حاوی گره حفره ی خاکستری می کند و بعد از آن گره حفره ی خاکستری بسته های داده را به صورت انتخابی کنار می گذارد. دومین نوع حمله ی حفره ی خاکستری، حمله ی حفره ی خاکستری هوشمند است که نوعی از شماره دنباله ی تشکیل دهنده ی حمله ی حفره ی خاکستری می باشد. گره در این مدل، در زمان روند شناسایی مسیر، به طور عادی رفتار می کند و سپس بخش هایی از بسته های داده را کنار می گذارد. گره حفره ی خاکستری به روشی غیرقابل پیش بینی در شبکه رفتار می کند و از همین رو، شناسایی این حمله ها دشوارتر از حمله های سیاه چاله است. لازم به ذکر است که گره سیاه چاله تمام داده های دریافت شده را کنار می گذارد. همان طور که در زیر بخش های 2.1 و 2.2 نشان داده شده، فرایندی را به منظور راه اندازی حمله ی حفره ی خاکستری هوشمند مطرح کرده ایم. گره حفره ی خاکستری هوشمند، در ابتدا در جهت مشارکت عادی در روند شناسایی مسیر ساخته می شود تا مسیر های به سمت مقصد را پیدا کند اما هنگامی که بسته ی داده را دریافت می کند، کنترل می کند که متغیر مورد اعتماد صحیح یا غلط است. اگر حمله ی حفره ی خاکستری هوشمند بین زمان های T1 و T2 راه اندازی شود، متغیر مورد اعتماد، روی غلط تنظیم می شود و بعد از آن گره کتار گذاشتن انتخابی بسته را اجرا می کند در غیر اینصورت بسته های داده را به گره بعدی و یا به گره مقصد ارسال می کند.
3. کارهای مرتبط
طرح های متعدد موجودی وجود دارند که از طرف بسیاری از محققین به منظور اداره کردن حمله کنار گذاشتن بسته ی انتخابی مطرح شده اند.
نویسنده در 17 روشی ارائه می کند که زنجیره ی گره های مخرب جمعی را مشخص می کند، این گره های مخرب، کنارگذاری انتخابی بسته در شبکه را اجرا می کنند. در این رویکرد، ترافیک داده ی کل به چندین بلوک با اندازه ی کوچک تقسیم می شود. گره منبع یک پیام مقدمه قبل از فرستادن داده به گره مقصد ارسال می کند تا آن را در مورد بلوک داده ی در حال آمدن، آگاه کند و زمان سنج را راه اندازی می کند. بعد از ارسال کردن پیام مقدمه، به منظور نظارت بر فعالیت های گره بعدی یک پیام نظارت به همه ی گره های همسایگی خود مخابره و ارسال بسته های داده را شروع می کند. از سوی دیگر، گره مقصد، یک پیام مقدمه ارسال می کند که شامل تعدادی از بسته های داده های دریافت شده از طرف گره مقصد است. اگر گره منبع، پیام مقدمه را در سر رسید زمان سنج دریافت کند، تعداد بسته های دریافت شده را با تعداد کل بسته های ارسال شده از طرف خودش را کنترل می کند و اگر اختلاف در محدوده ای قابل قبول باشد، بلوک بعدی بسته ی داده را ارسال می کند، در غیر اینصورت، شروع به شناسایی گره مخرب می کند و بعد از ان گره مخرب را بوسیله ی جمع کردن پاسخ از گره های نظارت، از شبکه حذف می کند. این رویکرد به علت بسته های کنترل اضافی متعدد دارای مسیریابی مازاد زیادی می باشد که این موضوع نقطه ضعف این رویکرد است و نویسنده ارزیابی عملکرد رویکرد پیشنهادی را انجام نداده است.
در 18، گره های خاص با عنوان IDS ، در شبکه مستقر می شوند که توانایی استراق سمع از تراکنش های همسایگی اش را دارد.در این روش، تنها گره های مقصد اجازه دارند تا بسته ی پاسخ را در هنگام دریافت کردن بسته ی درخواست، ارسال کنند و گره های میانی از ارسال بسته ی پاسخ منع می شوند. قوانین خاصی براساس کارنکردن گره ها وجود دارد. گرهی که کار نمی کند به عنوان گره مخرب اعلام می شود. گره IDS ، مقدار مشکوک بودن گره های نزدیکش را بر اساس اختلاف غیر عادی بین بسته های درخواست (RREQs) و پاسخ (RREPs) انتقال داده از گره، نظارت می کند و افزایش می دهد. اگر یک گره میانی، گره مقصد نباشد و این گره هیچ گاه یک بسته ی درخواست را برای مسیری خاص مخابره نکرده باشد، لذا گره IDS (که در ان نزدیکی قرار دارد) مقدار شک خود را به اندازه ی 1 در جدول گره مشکوکش افزایش می دهد. هنگامی که مقدار مشکوک بودن یک گره بزرگتر از مقدار آستانه شود، گره IDS یک پیام مسدود کردن به همه ی گره های در شبکه مخابره می کند تا گره مشکوک را مسدود کنند و از به همین ترتیب گره مشکوک را از شبکه جدا کنند. اگر چه این رویکرد قادر به شناسایی حمله ی سیاه چاله و حمله ی حفره ی خاکستری بر مبنای شماره دنباله در شبکه است اما در مورد حمله ی حفره ی خاکستری هوشمند شکست می خورد. گره حفره ی خاکستری هوشمند به درستی در شناسایی مسیر شرکت می کنند و همچنین بسته ی درخواست را به این علت که قادر به شناسایی آن نیست ارسال می کند. لذا محدودیت این رویکرد می باشد.
در 12، نویسنده بوسیله ی به کار گیری گره های خاص، روش پژوهشی جدیدی را برای کاهش دادن اثر گره حفره ی خاکستری پیشنهاد کرده است که می توان سیستم شناسایی نفوذ (IDS) در شبکه را مثال زد. گره منبع درباره ی تعداد بسته ها ی که از طریق مسیر جایگزین ارسال خواهد کرد به گره مقصد اطلاع رسانی می کند. هر زمانی که گره مقصد تعداد دقیق بسته های داده را نگیرد، بسته ی درخواست جستجو را به گره ای که در فاصله ی دو هاپی از آن است، (QRREQ) ارسال می کند، منتظر بسته ی پاسخ جستجو (QRREP) می ماند. بسته ی پاسخ جستجو (QRREP) شامل داده درباره ی تعداد بسته های داده ی ارسال شده از طریق گره به هاپ همسایگی بعدی در مسیر اصلی می شود. هنگام دریافت کردن بسته ی پاسخ جستجو (QRREP)، گره مقصد تایید می کند که آیا گره هاپ قبل از گره مقصد، همه ی بسته های داده ای که از گره هاپ قبل از خود، دریافت کرده را باز پخش کرده است یا نه. زمانی که گره مقصد بفهمد که گره قبلی اش همه ی بسته های دریافت کرده از گره قبل خود را ارسال نکرده است، ورودی اش را به لیست مظنون تبدیل می کند و به گره های IDS نزدیک در مورد گره مورد ظن هشدار می دهد. گره های IDS به تراکنش گره مخرب گوش می کنند و هر زمانی که هر گونه ناهنجاری شناسایی کنند، پیام مسدود کردن را در شبکه مخابره می کنند. این پیام شامل هویت گره مخرب است. و سپس گره مخرب را از شبکه جدا می کنند. محدودیت این رویکرد این است که گره مخرب می تواند بعد از دریافت بسته ی جستجو به طور عادی رفتار کند و می تواند بسته های داده را ارسال کند که گره IDS به همین دلیل در وضعیتی نخواهد بود که بتواند آن را شناسایی کند.
Abstract
Mobile ad hoc network (MANET) is defined as the category of wireless network that is capable of operating without any fixed infrastructure. The main assumption considered in this network is that all nodes are trusted nodes but in real scenario, some nodes can be malicious node and therefore can perform selective dropping of data packets instead of forwarding the data packets to the destination node. These malicious nodes behave normally during route discovery phase and afterwards drop fractions of the data packets routed through them. Such type of attack is known as smart gray hole attack which is variation of sequence number based gray hole attack. In this paper, we have launched smart gray hole attack and proposed a new mechanism for mitigating the impact of smart gray hole attack. Mitigating Gray hole Attack Mechanism (MGAM) uses several special nodes called as G-IDS (gray hole-intrusion detection system) nodes which are deployed in MANETs for detecting and preventing smart gray hole attack. G-IDS nodes overhear the transmission of its neighbouring nodes and when it detects that the node is dropping the data packets which are greater than threshold value then it broadcast the ALERT message in the network notifying about the identity of malicious node. The identified malicious is then blocked from further its participation by dropping the request and reply packet. In order to validate the effectiveness of our proposed mechanism, NS-2.35 simulator is used. The simulation results show that the proposed mechanism performs slightly well as compared with the existing scheme under smart gray hole attack.
1 Introduction
Mobile ad hoc network (MANET) is a progressing and most pervasive technology in wireless network which is recognized as an infrastructure less network [1]. It is selfconfigurable, temporary and scalable type of networks [2]. These types of networks are suitable for critical operation such as battlefield, emergency rescue operation etc. where it is difficult to set up infrastructure based network [3]. In this type of network, each device not only acts as a host and but also as a router [4]. The routing protocol such as ad hoc on-demand distance vector (AODV) [5], Dynamic source routing (DSR) [6] etc. which are used for communication are based on assumption that all nodes are cooperative and trustworthy [7]. Therefore, the MANET routing protocols are highly vulnerable to various types of denial of service (DoS) attacks [8], particularly packet dropping attack. The packet dropping attack can be categorized as Full packet drop and Partial packet drop attack. The full packet drop attack is known as black hole attack and the partial packet drop attack is known as gray hole attack. In case of Full packet drop attack, the malicious node do not participate in route discovery process and try to attracts the data traffic by giving false routing information and drops all the data packet received by it whereas in case of Partial packet drop attack, the malicious node participates genuinely in the route discovery process and also forwards the genuine reply packet received from the destination. When the source node sends the data packets through the path which contains gray hole node, it drops some of the data packets and the performance of the network slightly degrades. Therefore, there is need to provide security in ad-hoc network for dealing with the attacks. In this paper, the main contribution is that we have proposed a new mechanism called as Mitigating Gray hole Attack Mechanism (MGAM) for reducing the impact of smart gray hole attack in the network.
The remainder of the paper is structured as follows. Sect. 2 describes different types of gray hole attack and the procedures for launching smart gray hole attack. In Sect. 3, we explained about various existing schemes for dealing with gray hole attack in MANET. In Sect. 4, we describes in detail about the working mechanism of proposed methodology. Section 5 discusses about the experimental parameters and analysis in NS-2. In Sect. 6, we shows the performance comparison of our approach with ABM. The advantages and shortcomings of proposed approach and conclusions are discussed in Sects. 7 and 8 respectively.
2 Gray hole attack
Gray hole attack or selective forwarding attack is denial of service attack [8, 9] which is variation of black hole attack in which initially the node do not appear as a malicious but later on turns into malicious one and drops selective data packets. There can be two types of possible gray hole attacks in the MANET as depicted in Fig. 1. The first type of gray hole attack is Sequence Number based gray hole attack which is introduced in [10] in which the node gives false route reply by sending high destination sequence number with minimum hop count to the source node The source node on receiving the reply packets starts sending the data packets through the route which contains gray hole node and then selectively drops the data packets. The second type of gray hole attack is Smart gray hole attack which is variation of sequence number based gray hole attack in which the node behaves normally during the route discovery process and then drops some fractions of the data packets. The gray hole node behaves in an unpredictable manner in the network and therefore, it is difficult to detect these attack [11, 12] than the black hole node where the malicious node drops all the received data packets [13–16]. In order to launch the smart gray hole attack, we have presented the procedure as shown in 2.1 and 2.2 subsections. Initially the smart gray hole node is made to participates normally in route discovery process in order to find the route towards the destination but when it receives the data packets, it checks whether the trusted variable is True or False. If smart gray hole attack is to be launched between Time T1 and T2, the Trusted variable is set to the False and then it performs selective packet drop otherwise it forwards the data packets to the next node or to the destination node.
3 Related work
There are many existing schemes which have been proposed by many researchers for dealing with selective packet dropping attack.
The author in [17] proposed a technique that can detects chain of collaborative malicious nodes which performs selective packet drop in the network. In this approach, the total data traffic is divided into some small sized blocks. The source node sends a prelude message to the destination node before sending a block of the data to notify it about the incoming data block and starts the timer. After sending prelude message, it broadcasts a monitor message to all its neighbour nodes to monitor the activities of the next node and begins with the transmission of data packets. On the other hand, the destination node sends a postlude message which contains the number of data packets received by destination node. If the source node receives the postlude message within the expiry of timer, it checks the number of received packet with the total number of sent packet by it and if the differences is within the tolerable range, it sends the next block of the data packet else it starts detection of malicious node and then remove malicious node from the network by collecting the responses from the monitoring nodes. The drawback of this approach is that it has high routing overhead due to various extra control packets and the author has not done performance evaluation of the proposed approach.
In [18], special nodes called as IDS nodes are deployed in the network which has the ability to overhear its nearby transmission. In this technique, only the destination nodes are allowed to send the reply packet on receiving the request packet and intermediate nodes are forbidden to send the reply packet. There are certain rules according to which if nodes does not works, it is declared as malicious node. The IDS node monitors and increases the suspicious value of its nearby node according to abnormal difference between requests (RREQs) and replies (RREPs) packets transmitted from the node. If any intermediate node is not the destination node and that has never broadcasted a request packet for a specific path, but forwarded a reply packet for the path, then nearby IDS node will increment its suspicious value by 1 in its suspicious node table. When the suspicious value of a node becomes greater than the threshold value, IDS nodes broadcast a block message to all nodes in the network for blocking suspicious node and thus isolating it from the network. Although this approach is able to detect the black hole attack and sequence number based gray hole attack in the network but it fails in case of smart gray hole attack. The smart gray hole node participates correctly in route discovery and also forwards the request packet due to which it is unable to detect it and hence is the limitation of this approach.
In [12], the author has proposed a new methodology for mitigating the effects of the gray hole node by employing special nodes i.e. intrusion detection system (IDS) in the network. The source node intimates to the destination node about the number of packets it will forward through alternative path. Whenever the destination node does not get the actual number of data packets, it transmits query request (QRREQ) packet to the node which is at a distance of 2- hop from it and waits for the query reply (QRREP) packet. The query reply (QRREP) packet contains data about the number of data packets forwarded by the node to its next hop neighbor in the source route. On receiving the query reply (QRREP) packet, the destination node verifies whether its previous hop node has relayed all the data packets that it received from its previous hop node. When the destination node found that its previous node has not forwarded all the packets received from its previous node, it makes its entry into suspected list and alert to the nearby IDS nodes about the suspected node. The IDS nodes listens to the malicious node’s transmission and broadcast the block message in the network which contains the identity of malicious node whenever it detects any anomaly and then isolates the malicious node from the network. The limitation of this approach is that the malicious nodes can behave normally after receiving the query packet and can forward the data packets due to which the IDS node would not be in position to detect it.
چکیده
1. مقدمه
2. حمله حفره خاکستری
2.1. عملیات اجرا شده بوسیله ی گره های مخرب روی بسته ی درخواست دریافت
2.2. عملیات اجرا شده بوسیله ی گره های مخرب روی بسته ی درخواست دریافت
3. کارهای مرتبط
4. سیستم شناسایی نفوذ حفره ی خاکستری مطرح شده ی G-IDS
4.1. تعریف روش پژوهشی پیشنهاد شده
4.2. الگوریتم
4.2.1. اقدام انجام شده بوسیله ی گره های G-IDS در حالت استراق سمع
4.2.2. اقدام انجام شده بوسیله ی گره های G-IDS هنگام دریافت بسته ی هشدار
4.2.3. اقدام انجام شده بوسیله ی گره ها در هنگام دریافت بسته ی هشدار
4.2.4. اقدام انجام شده بوسیله ی گره ها در هنگام دریافت بسته ی درخواست
4.2.5. اقدام انجام شده بوسیله ی گره ها در هنگام دریافت بسته ی پاسخ
5. تحلیل و تنظیم محیطیِ عملی
5.1. معیار های عملکرد
5.1.1. نرخ انتقال بسته
5.1.2. نرخ اتلاف بسته
5.1.3. توان عملیاتی میانگین
5.1.4. مازاد مسیریابی
5.1.5. بار مسیریابی نرمالیزه شده
5.1.6. نرخ مثبت واقعی
5.1.7. نرخ مثبت غلط
5.2. نرخ انتقال بسته
5.3. نرخ اتلاف بسته
5.4. توان عملیاتی میانگین
5.5. مازاد مسیر یابی
5.6. بار مسیر یابی نرمالیزه شده
5.7. نرخ مثبت واقعی و نرخ مثبت غلط
6. مقایسه ی عملکرد با طرح موجود
6.1. نرخ انتقال بسته
6.2. نرخ اتلاف بسته
6.3. توان عملیاتی میانگین
6.4. مازاد مسیر یابی
6.5. بار مسیریابی نرمالیزه شده
6.6. نرخ مثبت واقعی و نرخ مثبت غلط
7. مزایا و معایب رویکرد پیشنهاد شده
8. نتیجه گیری
منابع
Abstract
1 Introduction
2 Gray hole attack
2.1 Action performed by malicious nodes on receiving request packet
2.2 Action performed by malicious nodes on receiving data packets
3 Related work
4 G-IDS -proposed grayhole intrusion detection system
4.1 Proposed methodology description
4.2 Algorithm
4.2.1 Action performed by G-IDS nodes in sniff mode
4.2.2 Action performed by G-IDS nodes on receiving ALERT packet
4.2.3 Action performed by nodes on receiving ALERT packet
4.2.4 Action performed by nodes on receiving request packet
4.2.5 Action performed by nodes on receiving reply packet
5 Experimental environmental setup and analysis
5.1 Performance metrics
5.1.1 Packet delivery rate
5.1.2 Packet loss rate
5.1.3 Average throughput
5.1.4 Routing overhead
5.1.5 Normalized routing load
5.1.6 True positive rate
5.1.7 False positive rate
5.2 Packet delivery rate
5.3 Packet loss rate
5.4 Average throughput
5.5 Routing overhead
5.6 Normalized routing load
5.7 True positive and false positive rate
6 Performance comparison with existing scheme
6.1 Packet delivery rate
6.2 Packet loss rate
6.3 Average throughput
6.4 Routing overhead
6.5 Normalized routing load
6.6 True positive and false positive rate
7 Advantages and shortcomings of proposed approach
8 Conclusion
References
