
دانلود رایگان مقاله تکنیک های رمزگذاری تصویر
چکیده
رمزگذاری عکس نقش مهمی در تضمین انتقال طبقه بندی شده و ظرفیت عکس در وب بازی می کند. پس از رمزگذاری در زمان مناسب، عکس تحت آزمون مهمی قرار می گیرد زیرا هر عکس شامل اطلاعات اندازه گیری شده ی گسترده ایی است. این مقاله به بررسی رمزگذاری عکس در فضا و در محدوده های فرکانس و هیبریدی- با در نظر گرفتن هر دو استراتژی رمزگذاری کامل و رمز گذاری انتخابی- می پردازد.
1. مقدمه
رمزنگاری در مورد مکاتبات در منطقه ی دشمن است و مسائل مختلف مثل رمزگذاری ، بررسی و تخصیص کلید به صورت یک زوج را شامل می شود. زمینه ی رمزنگاری فعلی مبتی بر یک تئوری اصولی است که براساس آن می توان این مسائل را درک کرد. رمزنگاری بهترین روش برای ارزیابی سنت هاست است، به این صورت که آن ها را استنباط می کند و به چگونگی ایجاد سنت هایی که می توان به آن ها اعتقاد داشت، می پردازد.
داده های رسانه ایی که به طور اتواتیک توسعه یافته اند،به صورت گسترده در دسترس هستند. اخیرا، تجهیز رسانه در عمل و در جهت امنیت مربوط به داده ی صوتی و تصویری ضرورت یافته است و نگرانی هایی در مورد استاندارد این تجهیز وجود دارد. شناسایی مسائل اساسی پیرامون موضوع رمزگذاری انجام شده و بیشتر روی استراتژی های رمزگذاری عکس و نظارت روی مکاتبات حاضر با استفاده از روش های آشوبی تمرکزشده است.
رمزگذاری عکس آشوبی می تواند به وسیله ی ویژگی های آشوبی شامل المان های قطعی، رفتار نامنظم و ایجاد تغییرات غیر مستقیم ساخته شود. با این استدلال، در مسائل معمولی ضمن داشتن محدودیت های امنیتی، بررسی های دیداری تسریع می شود، که این موضوع ممکن است در یک زوج از درخواست ها مناسب باشد.
تصاویر خودکار بزرگترین بخش مورد استفاده به عنوان بخشی از دستورهای گوناگون که ارتش را نظم می دهد، چهارچوب های کاری مفید و حقیقی هستند که دسترسی به آن ها باید به صورت کنترل شده انجام شود. این چهارچوب ها ابزارهایی برای اثبات درست بودن عکس ها ارائه می دهند.
قدیمی ترین و مهم ترین مسئله در رمزنگاری، ایمنی ارتباط در یک کانال ضعیف است. بخش A باید به بخش B یک پیام رمز در طول خط مکاتبات بفرستد، که ممکن است به وسیله ی دشمن دریافت شود. پیشرفت های اخیر در مهندسی به ویژه در صنعت خودرو و مکاتبات، اجازه ی تجارت های بزرگ جهت مناسب سازی محاسبات انجام شده برای محتوای رسانه از طریق اینترنت را صادر کرد.
پس از آن با افزایش آرشیوهای پیشرفته ، لوازم بررسی عکس و قابلیت دسترس در اینترنت، شرایط برای کپی رایت در داده های رسانه ایی مثل عکس، محتوا، صدا و ویژگی های محتوایی فراهم شد.
در حال حاضر یک آزمون متناوب جهت ایمن سازی روش های جدید- که دارای مجوز باشند- در سیستم های صوتی و تصویری انجام می شود.
برای مدیریت مسائل خاص، دو پیشرفت چشمگیر جهت ایجاد امنیت در عکس ها حاصل شده است که عبارتند از: آ) استفاده از روش های رمز گذاری عکس که امنیت کاملی ایجاد می کند، وقتی از مفاهیم پیشرفته در تعدادی از سیستم های پخش استفاده می شود و ب)استفاده از سیستم های چاپ سفید به عنوان ابزاری در جهت بیمه کردن در برابر کپی رایت ، برخورداری از حق مالکیت و بازبینی. در این مقاله ، به طور جدی روی روش های رمز گذاری تصویر در نقشه های آشوبی آزمایش شده تمرکز شده است.
امنیت رسانه به عنوان قانونی جهت تامین امنیت داده های صوتی و تصویری با استفاده از یک سیستم یا یک مجموعه از روش های مورد استفاده مطرح می شود. این سیستم ها عمدتا روی رمزنگاری متمرکز هستند و هر نوع امنیت مربوط به مکاتبات ، یا امنیت در برابر دستبرد( مدیریت حقوق دیجیتال و واترمارکینگ) یا هر دو را تقویت می کنند.
Abstract
Image encryption plays a paramount part to guarantee classified transmission and capacity of image over web. Then again, a real-time image encryption confronts a more noteworthy test because of vast measure of information included. This paper exhibits an audit on image encryption in spatial, frequency and hybrid domains with both full encryption and selective encryption strategy.
1 Introduction
Cryptography is about correspondence in the region of an adversary. It joins various issues like encryption, check, and key assignment to name a couple. The field of current cryptography gives a theoretical stronghold centered around which one can fathom what definitely these issues are, the best approach to evaluate traditions that infer to light up them and how to gather traditions in whose security one can have conviction [1].
Advanced automated advances have made media data by and large available. Starting late, media procurements get essential in practice and along these lines security of sight and sound data has gotten standard concern. The central issues identifying with the issue of encryption has been inspected and moreover an outline on picture encryption strategies centered on chaotic techniques have been overseen in the present correspondence.
The chaotic image encryption could be made by using properties of chaos including deterministic elements, erratic conduct and non-straight change. This thought prompts routines that can in the meantime give security limits and a general visual check, which may be suitable in a couple of demands.
Automated pictures are for the most part used as a piece of diverse orders, that join military, genuine and helpful frameworks and these procurements need to control access to pictures and give the means to affirm uprightness of images.
The most aged and fundamental issue of cryptography is secure communication over a shaky channel. Party A needs to send to gathering B a mystery message over a correspondence line, which may be tapped by an enemy. The late developments in engineering, particularly in machine industry and correspondences, permitted possibly tremendous business for appropriating computerized interactive media content through the Internet.
Then again, the multiplication of advanced archives, picture handling apparatuses, and the overall accessibility of Internet access has made a perfect medium for copyright misrepresentation and wild appropriation of media, for example, picture, content, sound, and feature content [2].
An alternate significant test now is the manner by which to secure the licensed innovation of media substance in sight and sound systems.
To manage the specialized difficulties, the two significant picture security advances are underutilize: (a) Image encryption procedures to give end-to-end security when dispersing advanced substance over a mixture of disseminations systems, and (b) watermarking systems as an instrument to accomplish copyright insurance, proprietorship follow, and verification. In this paper, the flow research endeavors in picture encryption procedures focused around chaotic plans are examined.
Interactive media security as a rule is given by a system or a set of techniques used to secure the sight and sound substance. These systems are intensely focused around cryptography and they empower either correspondence security, or security against robbery (Digital Rights Management and watermarking), or both.
چکیده
1.مقدمه
2. مقدمات
2.1. متن ساده
2.2. متن رمزی
2.2.1. رمزها
2.2.2. کدها
2.3. رمزگذاری
2.4. رمزگشایی
2.5. کلید
2.6. هدف از رمز نگاری
2.6.1. محرمانه بودن
2.6.2. تایید کردن
2.6.3. امانت داری
2.6.4. انکارناپذیربودن
2.6.5. کنترل دسترسی
2.7. دسته بندی رمزنگاری
2.7.1. رمزگذاری متقارن
2.7.1.1. رمزهای قفل
2.7.1.2. رمزهای رشته
2.7.1.1. رمزهای قفل
2.7.1.1.2. تعریف
2.7.1.1.3. تعریف
2.7.1.2. رمزهای رشته ایی
2.7.1.2.1. رمزهای رشته ایی سنکرون
2.7.1.2.2. رمزهای رشته ایی خود سنکرون
2.7.2. رمزگذاری نامتقارن
2.8. انتشار و در هم ریختگی
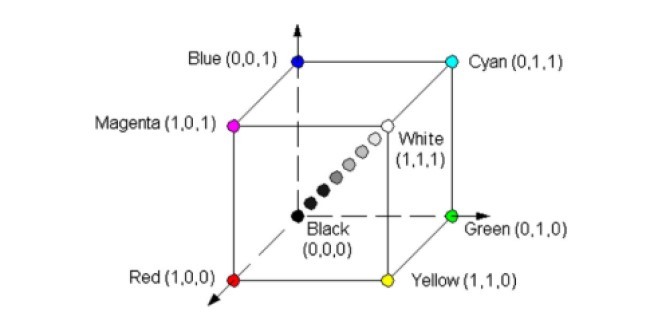
2.9. فضا و محدوده ی فرکانس
2.9.1. محدوده ی فضایی
2.9.2. محدوده ی فرکانس
2.9.2.1. مولفه های فرکانس
2.9.2.2. مولفه های فرکانس بالا
2.9.2.3 مولفه های فرکانس پایین
2.9.3 تفاوت بین محدوده ی فضایی و محدوده فرکانس
3. مروری بر مقالات پیرامون روش های رمزگذاری عکس
3.1. رمزگذاری کامل
3.1.1. محدوده ی فضایی
3.1.2. محدوده ی فرکانس
3.1.3. محدوده ی هیبریدی
3.2. رمزگذاری انتخابی
3.2.1. محدوده ی فضایی
3.2.2. محدوده فرکانس
3.2.3 . قلمرو هیبریدی
4. نتایج
منابع
Abstract
1 Introduction
2 Preliminaries
2.1 Plain Text
2.2 Cipher Text
2.2.1 Ciphers
2.2.2 Codes
2.3 Encryption
2.4 Decryption
2.5 Key
2.6 Purpose of Cryptography
2.6.1 Confidentiality
2.6.2 Authentication
2.6.3 Integrity
2.6.4 Non Repudiation
2.6.5 Access Control
2.7 Classification of Cryptography
2.7.1 Symmetric Encryption
2.7.1.1 Block ciphers
2.7.1.2 Stream ciphers
2.7.1.1 Block ciphers
2.7.1.1.2 Definition
2.7.1.1.3 Definition
2.7.1.2 Stream Ciphers
2.7.1.2.1 Synchronous Stream Ciphers
2.7.1.2.2 Self-synchronizing Stream Ciphers
2.7.2 Asymmetric Encryption
2.8 Diffusion and Confusion
2.9 Spatial and Frequency Domain
2.9.1 Spatial Domain
2.9.2 Frequency Domain
2.9.2.1 Frequency Components
2.9.2.2 High Frequency Components
2.9.2.3 Low Frequency Components
2.9.3 Difference Between Spatial Domain and Frequency Domain
3 Literature Review of Image Encryption Techniques
3.1 Full Encryption
3.1.1 Spatial Domain
3.1.2 Frequency Domain
3.1.3 Hybrid Domain
3.2 Selective Encryption
3.2.1 Spatial Domain
3.2.2 Frequency Domain
3.2.3 Hybrid Domain
4 Conclusions
References
