
دانلود رایگان مقاله سیستم خدمات آرشیو شخصی با استفاده از تکنولوژی بلاک چین
چکیده
این مقاله برای کاوش کاربردهای تکنولوژی بلاک چین تا مفهوم «اثبات X»، همانند اثبات هویت، اثبات مالکیت اموال، اثبات معامله خاص، اثبات درجه علمی، اثبات رکوردهای پزشکی، اثبات موفقیت های دانشگاهی و غیره می-باشد. این مقاله رویکرد نوین ایجاد یک سیستم خدمات و مدیریت آرشیو شخصی تغییرناپذیر، شفاف، غیرمتمرکز و ایمن را توصیف می کند. آرشیو شخصی به عنوان کلکسیونی از مصنوعات متعدد تعریف شده است که نمونه کارهای شخصی و نیز هویتهای منحصر به فرد شخصی را منعکس می کند. نمونه کارهای شخصی فراتر بیان موفقیت شخصی می باشد. این (نمونه کارها) یک سند مستند طراحی شده برای ارائه اسناد و مثالهای کیفی و کمی می باشد. موضوعات می توانند اطلاعات خود را با اثبات تگ کنند به طوری که توسط نهادها یا سازمانهای مورد اعتماد همانند دانشگاهها مورد تائید قرار گیرند. چنین اثباتهایی همراه با سطوح محرمانگی می باشند که در حوزه های عمومی به نمایش در آمدند. هویتهای شخصی شامل بیومتریکها و نیز دیگر چند فاکتوریها همانند چیزی که فاعل «دارای» آن می باشد، فاعل آن را «می داند» یا فاعل به آن «عمل» می کند. ذینغعان در یک کنسرسیوم با رویکرد شبکه بلاک-چین به عنوان تصدیق کنندگان و یا ماینرهایی عمل می کنند که به خدمات مورد اعتماد آنها اجماع توزیع شده ارائه می کنند. چنین سیستم مبتنی بر آرشیو شخصی می تواند تا اپلیکیشنهای متعدد از جمله شبکه های حرفه ای همانند لینکدین، تائید اعتبار آنی همانند alipay یا انسان زنده از باتهای اجتماعی همانند رسانه اجتماعی اینترنت بسط داده شود. شبیه سازی نمونه الگو (پروتوتایپ) نشان می دهد که مدیریت چنین نمونه کارهای شخصی و سیستم خدمات ممکن بوده و در برابر حملات ID بسیاری مصون می باشد.
1-مقدمه
سیستم خدمات آرشیو شخصی (PASS) به عنوان کلکسیونی از مصنوعات دیجیتالی و نیز کلکسیونی از ابزارهای خدماتی تعریف شده است. مصنوعات دیجیتالی شخصی (PDA) یک شکل دیجیتال از دستاوردهای شخصی با اسناد مستند (PAE) یا هویتهای شخصی (PID) می باشد می تواند برای شناسایی منحصر به فرد یک شخص استفاده شود. مثالهایی از PAE عبارتند از آموزش شخصی، تجربیات، درجه (مدرک)، آموزش و یادگیری، دیپلم، نسخه های دانشگاهی (آکادمیک) و گواهی های متعدد. ثروت شخصی همانند ارزش دارایی، موجودی بانکی و سرمایه گذاریها نیز می توانند مثالهای یاز PAE باشند. مثالهای معمول PID عبارتند از سنجشهای بیومتریک از شخص (فرد) همانند اثرات انگشت، عنبیه و رگ. اطلاعات دیگری که تنها شخص از آنها آگاه می باشد، اشیاء فیزیکی که شخص مالک آنها می باشد، می توانند مثالهایی از PID باشند. الگوهای رفتاری، بازتاب شخصی و خصوصیات نیز به عنوان مثالهایی از PID در نظر گرفته شدند.
کلکسیونی از PAEها مشابه با نمونه کارهای شخصی (PP) می باشند. این همراه با جدول زمانی می باشد که خصوصیات مخصوص یک شخص را شکل می دهند. PP یک شکل متمایزی از رزومه می باشد که بسیار انحصاری و جامع تر نسبت یک بیانات در رزومه است.
برای اینکه مفید و مورد اعتماد باشند، PDAها نیاز دارند تا توسط یک شخص ثالث مورد تائید قرار گیرند کسی که باید دانش این مصنوعات ادعا شده را راهنمایی کند. برای مثال، دانشگاه می تواند نسخه های (متون) رسمی به فارغ التحصیلان خود ارائه کند. مالک یک زمین قادر به ارائه یک نامه مرجع به مستاجرین خود ارائه کند. هیچ نهاد دیگری نمی تواند این را انجام دهد.
نقش های متعددی را در این فرآیند تعریف کردیم. از عبارت «فاعل» به عنوان شخص یا کاربری استفاده می کنیم که در حال ایجاد کلکسیون PDAهای خود می باشد، «گواهی دهنده» یا «مرجع صدور گواهی» موسسه یا نهادی که گواهی ارائه می کند، «مفتش » آژانس یا سازمانی می باشد که خدمات بررسی و جمع آوری ادله های مرتبط با هرگونه موضوعات خاص را عهده دار می باشد و «کلاینت» یا «مشتری» شخص یا سازمانی می باشد که از خدمات حرفه ای ارائه شده توسط «مفتش » استفاده می کند. برای مثال، برای استخدام یک کاندید بالقوه توسط یک کمپانی، کاندید فاعل می باشد، کمپانی مشتری می باشد که نیازمند استخدام یک شخص ثالث برای اعتبارسنجی تمام اطلاعات ارائه شده توسط فاعل است. این شخص ثالث مفتش بوده و کمپانی مشتری مفتش می باشد. مفتش نیاز دارد تا با مراجع صدور گواهی متعدد همانند دانشگاهها تماس حاصل کند کسی که آموزش را ارتقاء می دهد، کمپانی هایی که برای کار استفاده شدند یا سازمانهایی که گواهی های دیگری صادر می کنند.
این فرآیند اعتبارسنجی PDAها از سوی مفتش (یا بازپرس) اغلب زمانبر می باشد. همچنین این فرآیند هر بار که مشتری درخواست ارائه می کند، تکرار می شود. در برخی موارد، این فرآیند اطلاعات فراتر از رضایت ارائه شده توسط فاعل فراهم می کند. بنابراین، حاوی تهدید حریم خصوصی می باشد. به علاوه، این فرآیند اساسا یک مدلی از سیستم متمرکز می باشد که می تواند به طور بالقوه مسبب یک نقطه شکست، یک نقطه تنگنا، یک نقطه سردرگمی و نقطه سوء استفاده شود. برای مثال، اجازه آموزش در هنگام استخدام یک یار کمکی (وردست) توسط شخص ثالث زمان بر می باشد. در برخی موارد حدی، تجربه کردیم که ترم شروع شده است در حالیکه این اجازه هنوز در حالت تعلیق می باشد. مثال دیگر درباره نام تغییر داده شده توسط فاعل می باشد. بدون آشکارسازی نام قبلی آن، تائید فاعل سخت می باشد. موردی را می بینیم که فاعل از یک موسسه می خواهد تا دیپلم جدید به دلیل تغییرنام صادر کند. این معمولا یک ماموریت غیرمحتمل می باشد اگرچه در این مورد فاعل تمام دیگر IDها را دارا می باشد که به همان شکل باقی می مانند و تنها نام متفاوت می باشد.
اما، فرآیند اعتبارسنجی (تائید) بسیار ضروری می باشد و باید انجام شود. مشاهده می کنیم که پدینگ رزومه بسیار فراگیر شده است [1]. پدینگ رزومه افزودن اطلاعات غلط یا اغراق شده به رزومه جهت ارتقاء شانس برای یک شغل می باشد. بیش از 40 درصد رزومه ها حقوق خود را افزایش می دهند، 33 درصد توصیف ناصحیح از شغل دارند، 29 درصد تاریخ های اشتغال را تغییر می دهند، 27 درصد رفرنسها را جعل می کنند و 21 درصد مدارک را جعل می کنند. از این رو، می توانیم تصور کنیم که مسئولیت الزام تائید اعتبار بسیار سنگین می باشد.
اخیرا، تکنولوژی بلاک چین که در ابتدا در بیت کوین [20] به عنوان یک شبکه پرداخت نوآورانه و نوع جدید از پول معرفی شد، در صنایع مرتبط با امور مالی مورد استفاده قرار گرفته است. زمینه های دیگر بسیاری همانند زنجیره تامین، تولید و اینترنت اشیاء نیز در حال استفاده از آن می باشند. [برای مثال مراجع 21 و 22]. خصوصیات کلیدی از استفاده از تکنولوژی بلاک چین عبارتند از غیرمتمرکز بودن، سرفصل مشترک مبتنی بر اجماع، قرارداد هوشمند، شفافیت بالا و حریم خصوصی قوی. ایده ذخیره و انتقال ایمن اسناد امضاء شده به صورت دیجیتال با یک دنباله ممیزی فوق العاده در شبکه های تبادل سند تغییرناپذیر در تجارت مالی، حمل و نقل و بیمه در حال ظهور می باشد جایی که هرکس دارای تقاضای مشابه برای اعتبارسنجی هویت افراد و دارایی ها می باشد. این نیازمند شخص ثالث به عنوان یک میانجی (واسطه) یا نهاد برای اعتبارسنجی، تمیز کردن خانه یا هر هدف دیگر نمی باشد. این در ایجاد یک سرویس ID تغییرناپذیر ناشناس ایمن و هنوز شفاف مورد استفاده قرار می گیرد [33].
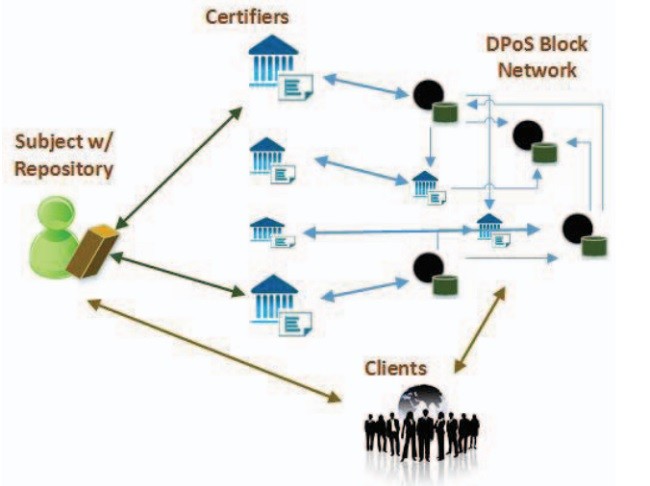
سیستم خدمات آرشیو شخصی (PASS) پیشنهادی در این مقاله برای استفاده از تکنولوژی بلاک چین جهت بکارگیری خصوصیات مطلوب آن همانند تغییرناپذیری، شفافیت، ناشناسی و اجماع عمومی می باشد. فاعل PDAهای خود را کنترل می کند و تصمیم می گیرد که این PDAها در اختیار چه کسی قرار دهد. شکل1 زیرساختار عمومی (کلی) و نمای معماری یک PASS تحت بلاک چین را نشان می دهد. فاعل، که به وسیله یک آیکون نشان داده شده است، مخزن خود را دارد که تمام PDAهای مربوطه خود جمع آوری می کند. گواهی دهنده ها گواهی ها را به صاحبان آنها و نیز به شبکه مورد اعتماد صادر می کنند. چنین گواهی هایی فقط یکبار برای تمام افراد درگیر صادر می شوند و دیگر نباید صادر شوند. هیچ نیازی برای حضور شخص ثالث یا مفتش وجود ندارد. آنها (مراجع صدور گواهی) همچنین گواهی ها را به شبکه بلاک چین با گرایش کنسرسیوم ارائه می کنند که اعتماد در آن به صورت اجماع نظر حاصل شده است. مشتری از فاعل درخواست می کند و به PDAهای اعطا شده دسترسی پیدا می کند.
Abstract
This paper is to explore applications of the blockchain technology to the concept of “proof of X” such as proof of identity, proof of property ownership, proof of specific transaction, proof of college degree, proof of medical records, proof of academic achievements, etc. It describes a novel approach of building a decentralized transparent immutable secure personal archive management and service system. Personal archive is defined as a collection of various artifacts that reflect personal portfolio as well as personal unique identifications. Personal portfolio is beyond of a statement of personal achievement. It is an evidentiary document designed to provide qualitative and quantitative chronically documents and examples. Subjects can tag their information with proof, that is, certified by trusted entities or organizations like universities. Such proofs are associated with confidentiality levels exposed in the public domains. Personal identifications include biometrics as well as other multi-factors such as something the subject “has”, the subject “knows” or the subject “acts”. Stack holders in a consortium oriented blockchain network serve as verifiers and /or miners that provide their trusted services the delegated proof of stake. Such personal archive based system can be exploited to various applications including professional network like Linkedin, instant credit approval like alipay or live human from social bots like internet social media. A prototype simulation shows that such personal portfolio management and service system is feasible and immune to many ID attacks.
I. INTRODUCTION
Personal archive service system (PASS) is defined as a collection of digital artifacts as well as a collection of service tools. A personal digital artifact (PDA) is a digital form of personal achievements with evidentiary documents (PAE) or of personal identifications (PID) that can be used to uniquely identify a person. Examples of PAE are such as personal education, experiences, training, degree, diploma, academic transcripts and various certificates. Personal wealth like property value, bank balance, investments can also be examples of PAE. Typical examples of PID are biometric measures from the person like finger prints, iris and vein. Other information known only to the person, physical objects owned by the person can be examples of PID. Behavior patterns, personal reflection and characteristics are also considered as examples of PID.
The collection of PAEs are similar to personal portfolio (PP). It is associated with timeline that assembles a specific characteristics of a person. PP is distinct from resume in that it is more of inclusive and expanding than a line of statements in resume.
To be useful and trustful, these PDAs need to be verified by a third party who should have direct knowledge of these claimed artifacts. For example, a university can provide official transcripts to their graduates. A landlord is able to provide a letter of reference to their tenants. No other entities can do that.
We define various roles in this process. We use the term “subject” to be a person or a user who is building his or her collection of PDAs, “certifier” to be an institute or an entity that provides certification, “inquisitor” to be an agent or organization who provides service of investigation and obtaining relevant proof of any particular subject, and “client” to a person or organization using professional services provided by “inquisitor”. For example, for a potential candidate to be hired by a company, the candidate is a subject, the company is a client who needs to hire a third party to verify all the information provided by the subject. The third party is the inquisitor and the company is a client of the inquisitor. The inquisitor needs to contact various certifiers such as universities who gain education, companies who used to work, or organizations who issue other certifications.
This process of verifying PDAs by inquisitors is often time consuming. It is also repeated every time a client makes a request. In some cases, it obtains information beyond the consent given by the subject. Therefore, it poses a threat of privacy. Moreover, it is essentially a model of centralized system that can potentially cause a point of failure, a point of bottleneck, a point of confusion and a point of abuse. For example, clearance for teaching when hiring an adjunct by a third party takes time. In some extreme cases we have experienced that the semester starts while the clearance is still pending. Another example is about name change by a subject. Without revealing its previous name used, the subject is hard to get verified. We see a case that a subject wants an institution to issue a new diploma due to name change. It is usually a mission impossible task although in this case the subject has all other IDs that remain the same just name difference.
But, the process of verification is becoming increasing necessary and a must. We have observed resume padding is becoming more epidemic [1]. Resume padding is to add false or exaggerated information to a resume to enhance credentials for a job. More than 40% of resumes inflates their salary, 33% inaccurate job description, 29% altered employment dates, 27% falsified references, and 21% fraudulent degrees. Hence, we can image that the burden of requiring verification is very heavy.
Recently, blockchain technology, first introduced in bitcoin [20] as an innovative payment network and a new kind of money, is being applied to financial related industrials. Many other fields such as supply chain, manufacture, Internet of Things are exploiting it as well. [21-22 for example]. The key features from using the blockchain technology are its decentralized, consensus based shared ledger, smart contract, high transparency yet high privacy. The idea to have secure storage and transmission of digitally signed documents with a super audit trail in immutable document exchange networks is emerging in trade finance, shipping, and insurance, where everyone has the same demand to validate the identity of people and assets. It does not need a third party as an intermediary or authority for verification, cleaning house or any other purposes. It is being used in building a secure anonymous yet transparent immutable ID Service [33].
Personal Archive Service System (PASS) proposed in this paper is to use blockchain technology to exploit its desirable features such as immutable, transparency, anonymous and public consensus. The subject controls its own PDAs and makes decision to whom to release. Figure 1 illustrates the general infrastructure and architecture view of a PASS under blockchain. The subject, represented by icon has its own repository or wallet that aggregates all its relevant PDAs. The certifiers issue certificates to its owners as well as to a trusted network. It does such certificates once for everyone involved and should not be bothered anymore. There is no need to have a third party or an inquisitor. They also pass the certificates to a consortium oriented block chain network that the trust is developed in a delegated proof of stake. A client makes a request to the subject and gain access to those granted PDAs.
چکیده
1-مقدمه
2- مرور منابع و مراجع
3- ساختار PASS
A-مصنوعات، نمونه کارها و آرشیو
B- ابزارهای سرویس
C- فاعل، مفتش ، مرجع صدور گواهی، مشتری، استیک
D- اعتماد اولیه و بلوک شبکه کنسرسیوم
E-دستیابی به اجماع توزیع شده در یک سیستم رمزنگاری شده
F- بیومتریکها و منحصر به فردی
4- ارتباطات PASS
5- سیستم سرویس
6- نتیجه گیری
Abstract
I.Introduction
II.Literature Review
III.Structure of Pass
A. Artifacts, Portfolio and Archive
B. Servcie Tools
C. Subject, Inquisitor, Certifier, Client, Stake
D. Initial Trust and Block of the Consortium Network
E. Delegated Proof of Stake (DPoS)
F. Biometrics and Uniqueness
IV.Communication of Pass
V.Service System
VI.Discussion
REFERENCES
