
دانلود رایگان مقاله مقایسه فن های طبقه بندی مورد استفاده برای تشخیص نفوذ شبکه
چکیده
در تحقیق قبلی، یک سیستم ایمنی مصنوعی چندگانه برای شناسایی و طبقهبندی نفوذ شبکه پیشنهاد و آزمایش شد که در آن یک فرایند تشخیص و طبقهبندی چندلایه روی هر عامل برای هر میزبان در شبکه اجرا شد. در این مقاله، ما آزمایشهایی را انجام میدهیم که با طبقهبندیهای مختلف طبقهبندیهای مناسب را انتخاب کرده و آنها را مقایسه میکنیم تا دقت تشخیص را افزایش دهیم و اطلاعات بیشتری در مورد ناهنجاریهای تشخیصی به دست آوریم. نشان داده خواهد شد که به دلیل نرخهای مختلف طبقهبندی بهدستآمده، هیچ طبقهبندی نمیبایست برای تمام انواع حملات استفاده شود. این به خاطر نمایش حملات در مجموعه سلسله و وابستگی بین ویژگیهای مورداستفاده برای شناسایی آنها است. همچنین نشان داده خواهد شد که یک طبقهبندی کننده ساده و اساسی مانند Naive Bayes دارای نتایج طبقهبندی بهتر در مورد حملات کم نشان دادهشده است و درخت تصمیمگیری اولیه مانند درخت Naive-Bayes Tree و Best-First نتایج بسیار خوبی نسبت به J48 معروف (اجرای وکا C4.5) و درخت تصمیمگیری Random Forest ارائه میدهد. بر اساس این آزمایشها و نتایج آنها، طبقهبندی کنندههای Naive Bayes و Best-First برای طبقهبندی ترافیک ناشناخته انتخاب شدند. نشان دادهشده است که در مرحله تشخیص 90٪ ناهنجاریها شناساییشده و در مرحله طبقهبندی 88٪ از مثبتهای کاذب با موفقیت بهعنوان اتصالات ترافیکی عادی برچسبگذاری شده و 79٪ از حملات DoS و Probe بهدرستی توسط NB، NBTree و طبقهبندی کننده BFTree برچسبگذاری شدهاند.
1. معرفی
امروزه دستگاههای کامپیوتری معمولاً به هم متصل هستند که به دستگاههای توزیعشده بزرگ وصل هستند که در دنیای محاسبات صنعتی ضروری هستند. دستگاههای نرمافزاری امروز نیازمند روندهایی مانند اتصالات، هوش و فراگیری هستند که همگی منجر به ایجاد دستگاههای چند عامل شد. دستگاههای چندگانه رفتار هوشمندانه انسان و نحوه ارتباط انسانها با یکدیگر و با محیط آنها برای دستیابی به اهداف خاص را تقلید میکند. یکی از دستگاههایی که میتواند بهصورت موفقیتآمیز و کارآمد بهعنوان یک سیستمعامل چندگانه اجرا شود، دستگاههای ایمنی مصنوعی (AIS) است. سیستم ایمنی مصنوعی یک منطقه پژوهشی است که شامل ایمنیشناسی، علوم رایانه و مهندسی است. با الهام از دستگاههای ایمنی طبیعی، سه زمینه اصلی تحقیق تحت AIS قرار میگیرند: مدلسازی ایمنی، AIS های نظری و AIS های کاربردی. مدلسازی ایمن در مورد مدلهای ایمنی و شبیهسازی سیستم ایمنی است. پژوهش AIS های نظری در مورد توضیح و نفوذ به جنبههای نظری الگوریتمهای AIS، مدلهای ریاضی و عملکرد و تجزیهوتحلیل پیچیدگی آنها است. درنهایت، تحقیق AIS های کاربردی در مورد توسعه و اجرای الگوریتمها و دستگاههای کامپیوتری الهام گرفته از دستگاههای ایمنی است که از آنها برای انواع برنامههای کاربردی دنیای واقعی استفاده میشود.
با توجه به دستگاههای کامپیوتری میتوانیم بفهمیم که مفهوم خود/ غیر خود در قالب فعالیتها و عناصری معمولی/ غیرعادی اعمال میشود. دستگاههای تشخیص نفوذ (IDS) دستگاههای امنیتی قدرتمندی هستند که انواع مختلفی برای اهداف حفاظتی دارند. آنها ابزار امنیتی خاصی را جایگزین نمیکنند، بلکه بهجای آن، یک خط دفاعی در برابر نفوذها و تهدیدات از داخل سیستم (یک کامپیوتر یا یک شبکه) و همچنین از خارج- درست مانند سیستم ایمنی اضافه میکنند. IDS ها میتوانند به روشهای مختلف دستهبندی شوند، اما اساساً میتوان آنها را به IDS هایی مبتنی بر سوءاستفاده و ناهنجار تقسیم کرد. IDS های سوءاستفاده که همچنین بهعنوان مبتنی بر امضا یا دانش شناخته میشوند، بستگی به تشخیص نفوذ با استفاده از الگوهای نشاندهنده حملات شناختهشده دارد. این الگوها یا امضاها با رویدادها برای یافتن نفوذهای ممکن مقایسه میشوند. IDS های غیرمتعارف که همچنین بهعنوان IDS های مبتنی بر رفتار شناخته میشود، به ساخت یک نمایه بستگی دارد که رفتار طبیعی یک سیستم را با نظارت بر فعالیتهای آن در طول زمان نشان میدهد. سپس هر انحراف از آن نمایه، یک ناهنجاری است. نمایهها میتوانند ایستا یا پویا باشند و با استفاده از بسیاری از ویژگیهای سیستم توسعه مییابند.
با تنوع و پیچیدگی فنهای حمله، بسیاری از مسائل در رابطه با IDS ها رایج هستند که باید در هنگام ساخت IDS موردتوجه قرار گیرند [17]. شایعترین مسئله، استخراج مجموعهای از قوانین تخصصی است که در اغلب موارد از طریق یک متخصص انسانی بهخصوص با استفاده از IDS سوءاستفاده بهروز میشود. با تشخیص ناهنجاری، چنین مسئلهای با استفاده از نمایش مناسب و تعریف حملات حل میشود، بنابراین انواع مختلف حملات میتواند با استفاده از مجموعهای محدود از قوانین با تغییرات این قوانین شناسایی شود. یکی دیگر از مسائل، مربوط به آموزش مدلهای رفتاری است که معمولاً اطلاعات عادی یا دو مجموعه دادههای عادی و غیرعادی برای آموزش استفاده میشود. فنهای یادگیری ماشینی بیشتر برای آموزش و یادگیری استفاده میشود.
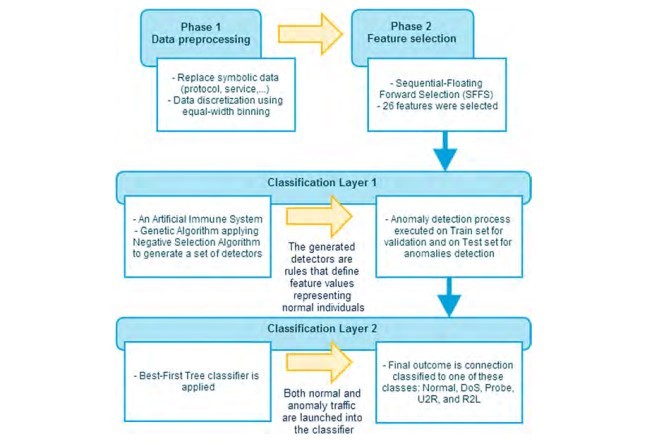
در تلاش برای غلبه بر مسائل ذکرشده در بالا، ما یک الگوریتم طبقهبندی دولایه با چندعاملی را پیشنهاد کردیم که ناهنجاریها را در یک شبکه تشخیص میدهد و طبقهبندی میکند. IDS سیستم پیشنهادی ترکیبی از الگوریتم ژنتیک با روش انتخاب منفی بهعنوان اولین لایه شناسایی ناهنجاریها است. سپس طبقهبندی کنندههای انتخابشده برای ترسیم ناهنجاریهای شناساییشده در هر دو ترافیک نرمال و غیرطبیعی آموزش داده میشود و بهکاربرده میشود. سیستم ایمنی یک سیستم توزیعی از سلولهای تخصصی متفاوتی است که دارای تعامل بالا بین اجزای آن برای یک پاسخ هماهنگ است. با توجه به این، بسیاری از رویکردها، اجرای یک AIS را بهعنوان یک سیستمعامل چندگانه پذیرفتهاند.
در تحقیقات قبلی که به نوعی به سیستم پیشنهادشده شبیه هستند، هر نوع طبقهبندی کننده خاص برای هر نوع حمله مورداستفاده قرار میگیرد، یا طبقهبندی کنندهها- که با استفاده از دادههای برچسبگذاری شده آموزش دادهشدهاند- بهطور مستقیم به مجموعه دادهها برای تشخیص نفوذ و برچسبگذاری حملات بدون برچسب اعمال میشود. سهم این مقاله این است که برخی تجزیهوتحلیل تطبیقی را برای پاسخ به سؤالات در مورد چگونگی عملکرد سیستم در پارامترهای مختلف انجام دهد و اینکه چه فنهایی برای بهترین نتایج و دلیل استفاده میشود. همچنین بررسی خواهد کرد که آیا تغذیه ترافیک عادی به طبقهبندی کنندهها اهمیت دارد یا خیر.
در یک گزارش از قبل منتشرشده [8] یک سیستم ایمنی مصنوعی چندگانه برای تشخیص و طبقهبندی نفوذ شبکه اعمال شد. الگوریتمی که بهعنوان یک فن سیستم ایمنی مصنوعی اعمالشده است، روش انتخاب منفی است که از الگوریتم ژنتیک استفاده میکند. بهعنوان یک سیستم هوشمند، دادهکاوی در طول فرایند برای بهترین نتایج استفاده میشود. دو طبقهبندی کننده برای طبقهبندیهای ناهنجاری، طبقهبندی کنندههای Bayes Naive Bayes و Best-First استفاده شد. طبقهبندی کننده Bayes Naive برای حملاتی استفاده شد که ارائه کمی در مجموعه دادههای آموزشی دارند، زیرا آنها ثابت کردهاند که نتایج بهتری نسبت به سایر طبقهبندی کنندهها در آزمایش قبلی داشتهاند. طبقهبندی کننده BFTree برای طبقهبندی حملات باقیمانده مورداستفاده قرار گرفت، زیرا آنها نتایج بهتری را نسبت به سایر طبقهبندی کنندههای پیچیدهتر در آزمایشها این مقاله نشان دادند.
مقاله بهصورت زیر مرتبشده است. بخش 2 زمینهای راجع به اصول فنهای طبقهبندی ارائه میدهد. در بخش 3 رویکرد پیشنهادی و مدل سیستم با اجزا و مرحلههای مختلف آن توضیح دادهشده است. بخش 4 شامل جزئیات آزمایش و تنظیمات است. نتایج در بخش 5 ارائهشده و موردبحث قرار میگیرد. درنهایت، نتیجهگیری باکار بیشتر در بخش 6 ارائه میشود.
ABSTRACT
In a previous research, a multi-agent artificial immune system for network intrusion detection and classification was proposed and tested, where a multi-layer detection and classification process was executed on each agent, for each host in the network. In this paper, we show the experiments that were held to chose the appropriate classifiers by testing different classifiers and comparing them to increase the detection accuracy and obtain more information on the detected anomalies. It will be shown that no single classifier should be used for all types of attacks, due to different classification rates obtained. This is due to attacks representations in the train set and dependency between features used to detect them. It will also be shown that a basic and simple classifier such as Naive Bayes has better classification results in the case of low-represented attacks, and the basic decision trees such as NaiveBayes Tree and Best-First Tree give very good results compared to well-known J48 (Weka implementation of C4.5) and Random Forest decision trees. Based on these experiments and their results, Naive Bayes and Best-First tree classifiers were selected to classify the anomaly-detected traffic. It was shown that in the detection phase, 90% of anomalies were detected, and in the classification phase, 88% of false positives were successfully labeled as normal traffic connections, and 79% of DoS and Probe attacks were labeled correctly, mostly by NB, NBTree, and BFTree classifiers.
1. Introduction
Computer systems today are usually interconnected, where they are networked into large distributed systems which are essential in industrial computing world. Today’s software systems require more trends such as interconnection, intelligence, and ubiquity. This all led to the arise of multi-agent systems. The multi-agent systems mimic human intelligent behavior, and the way humans interact with each other and towards their environment to achieve certain goals. One of the systems that can be implemented successfully and efficiently as a multi-agent system is Artificial Immune Systems (AIS). Artificial Immune System [1,11] is a research area that involves immunology, computer science, and engineering. Inspired by natural immune systems, three main fields of research lie under AIS: immune modeling, theoretical AISs, and applied AISs. Immune modeling is concerned about immunity models and immune systems simulations. Theoretical AISs research is about explaining and digging into the theoretical aspects of AIS algorithms, their mathematical models, and their performance and complexity analysis. Finally, applied AISs research is about developing and implementing algorithms and computers systems inspired by immune systems, applying them to a variety of real world applications.
Looking into computer systems, we can find that the self/non-self concept applies in the form of normal/anomalous activities and elements. Intrusion Detection Systems (IDS) are powerful security systems that have a variety of types for all protection purposes. They do not replace a certain security tool, but instead they add a defense line against intrusions and threats from inside the system (a computer or a network) as well as from outside – just like and immune system. IDSs can be categorized in different ways, but basically they can be classified into Misuse-based and Anomaly-based IDSs. Misuse IDS, which is also known as signature-based or knowledge-based, depends on detecting intrusions using patterns representing known attacks. These patterns or signatures are compared to captured events to find possible intrusions. Anomaly IDS, also known as behavior-based, depends on building a profile that represents normal behavior of a system by monitoring its activities over time. Then any deviation from that profile is considered an anomaly. Profiles can be static or dynamic, and are developed using many attributes of the system [13,17].
With the diversity and complexity of attacking techniques, many issues are common with IDSs that need to be considered while building an IDS [17]. The most common issue is deriving an expert rule set, which in most cases is updated through a human expert, especially with misuse IDS. With anomaly detection, such an issue is solved using proper representation and definition of attacks such that different types of attacks can be detected using a limited set of rules with variations of these rules. Another issue is the training of behavioral models, where usually normal data only is used for training or two sets of normal and anomalous data. Machine learning techniques are mostly used for training and learning.
In an attempt to overcome the mentioned issues above, we suggested a multi-agent, two-layer classification algorithm, that detects and classifies anomalies in a network. The suggested system IDS combines Genetic Algorithm with Negative Selection Approach as a first layer of anomalies detection. Then selected classifiers are trained and applied to label the detected anomalies in both the normal and anomalous traffic. The immune system is a distributed system composed of different specialized cells with high interactivity between its components to give a coordinated response. Taking this into consideration, many approaches adopted the implementation of an AIS as a multi-agent system.
In previous researches [14,16,19,22] that are similar some way to the suggested system, either specific classifiers are used for each attack type, or classifiers – which were trained using the labeled data – are applied directly to the data set for intrusion detection and labeling unlabeled attacks. The contribution of this paper is to do some comparative analysis to answer questions about how the system will act to different parameters, and which techniques to use for best results and why. It will also investigate whether it is rewarding to feed normal traffic into the classifiers or not.
In a previously published work [8], a multi-agent artificial immune system was implemented, for network intrusion detection and classification. The algorithm applied as an artificial immune system technique is Negative Selection Approach, using Genetic Algorithm. As an intelligent system, data mining is applied throughout the process for best results. Two classifiers were used for anomalies classification, Naive Bayes and Best-First Tree classifiers. Naive Bayes classifier was used for attacks that have low representation in the training data set as it has proven to give better results than other classifiers in a previous experiment. The BFTree classifier was used for the remaining attacks classification, as it also proved to give better results than other more complex classifiers in the experiments shown in this paper.
The paper is organized as follows. Section 2 presents a background about the basics of the classification techniques. In section 3, the proposed approach and system model is explained with its different components and phases. Section 4 includes the experiment details and settings. The results are presented and discussed in section 5. Finally, conclusion is given with future work in section 6.
چکیده
1. معرفی
2. فنهای طبقهبندی دادهها
2.1. طبقهبندی کننده Bayes Naïve
2.2. درختان تصمیمگیری
2.3. فرایندهای چندلایه
3. سیستم تشخیص و طبقهبندی دولایه
3.1. مرحله پیشپردازش داده
3.2. مرحله انتخاب ویژگی
3.3. لایه I: تولید ردیابها و تشخیص ناهنجاری
3.4. لایه دوم: استفاده از دستهبندی کنندهها برای دستهبندی حملات
4. آزمایشها
5. نتایج و بحث
5.1. نتایج طبقهبندی کنندهها
6. نتیجهگیری
منابع
ABSTRACT
1. Introduction
2. Data classification techniques
2.1. Naive Bayes classifier
2.2. Decision trees
2.3. Multi-layer perceptrons
3. The two-layer detection and classification system
3.1. Data preprocessing phase
3.2. Feature selection phase
3.3. Layer I: detectors generation and anomaly detection
3.4. Layer II: applying classifiers for attacks classification
4. Experiments
5. Results and discussion
5.1. Classifiers results
6. Conclusion
References
